
Unlocking the Power of Encrypted Data: Exploring the Best Uses of Fully Homomorphic Encryption
Compute on Confidential Information Without Decrypting: The Core Advantage of FHE
Key Insights on Fully Homomorphic Encryption Applications
- Enhanced Data Privacy: FHE allows computations directly on encrypted data, significantly reducing the risk of sensitive information being exposed during processing, especially in untrusted environments like the cloud.
- Secure Cloud Computing and Data Analytics: Businesses and organizations can leverage the scalability and power of cloud services for data analysis and storage without compromising the confidentiality of their data.
- Facilitating Secure Collaboration and Sharing: FHE enables multiple parties to perform computations on combined encrypted datasets without any party needing to reveal their raw data, opening doors for secure collaborative research and analysis.
Fully Homomorphic Encryption (FHE) represents a significant advancement in cryptography, offering the unique capability to perform computations directly on encrypted data without the need for decryption. This groundbreaking property addresses a critical challenge in data security and privacy: how to utilize sensitive information for analysis and processing without exposing it to potential breaches or unauthorized access. While traditional encryption methods protect data at rest and in transit, they require data to be decrypted for any operations to be performed, creating a vulnerability window. FHE eliminates this window, allowing data to remain encrypted throughout its lifecycle, even during active computation.
The Transformative Potential of Fully Homomorphic Encryption
The ability to compute on encrypted data has profound implications across numerous sectors. It enables organizations to maintain a higher level of data privacy and security, aligning with increasingly stringent data protection regulations and enhancing trust. The core idea is that a third party can perform computations on encrypted data and return an encrypted result, which can then be decrypted by the owner of the original data's secret key. The third party performing the computation never gains access to the unencrypted data or the final unencrypted result.
This concept can be illustrated with a simple analogy:
Traditional encryption is like a secure box with a lock. To do anything with the contents (data), you need to open the box (decrypt), perform the operation, and then potentially put the contents back and lock it again. During the time the box is open, the contents are vulnerable.
Homomorphic encryption, on the other hand, is like a special box with gloves built into it. You can manipulate the contents (data) and perform operations through the gloves without ever having to open the box (decrypt). The data remains protected inside the encrypted box at all times.
Understanding the Different Types of Homomorphic Encryption
While FHE is the most comprehensive form, it's helpful to understand its evolution:
Partially Homomorphic Encryption (PHE)
PHE schemes allow for only one type of mathematical operation (either addition or multiplication) to be performed on encrypted data. RSA encryption is an example of a partially homomorphic cryptosystem with respect to multiplication. While useful for specific, limited tasks, PHE does not support arbitrary computations.
An example of a serial data encrypter, showcasing hardware-based encryption.
Somewhat Homomorphic Encryption (SHE)
SHE schemes allow for both addition and multiplication operations on encrypted data, but only for a limited number of times or to a certain complexity level. As more operations are performed, noise in the ciphertext increases, which can eventually make decryption impossible. This limitation restricts the types and depth of computations that can be performed.
Leveled Fully Homomorphic Encryption (LHE)
LHE schemes support the evaluation of arbitrary circuits composed of multiple types of gates, but the depth of the circuit (the number of sequential operations) must be predetermined. While more flexible than SHE, it still requires some prior knowledge of the computation to be performed.
Fully Homomorphic Encryption (FHE)
FHE is the most powerful type, allowing for an unlimited number of additions and multiplications on encrypted data. This means any computable function can be evaluated on encrypted data without decryption. This was a significant breakthrough in cryptography, with the first plausible construction proposed by Craig Gentry in 2009.
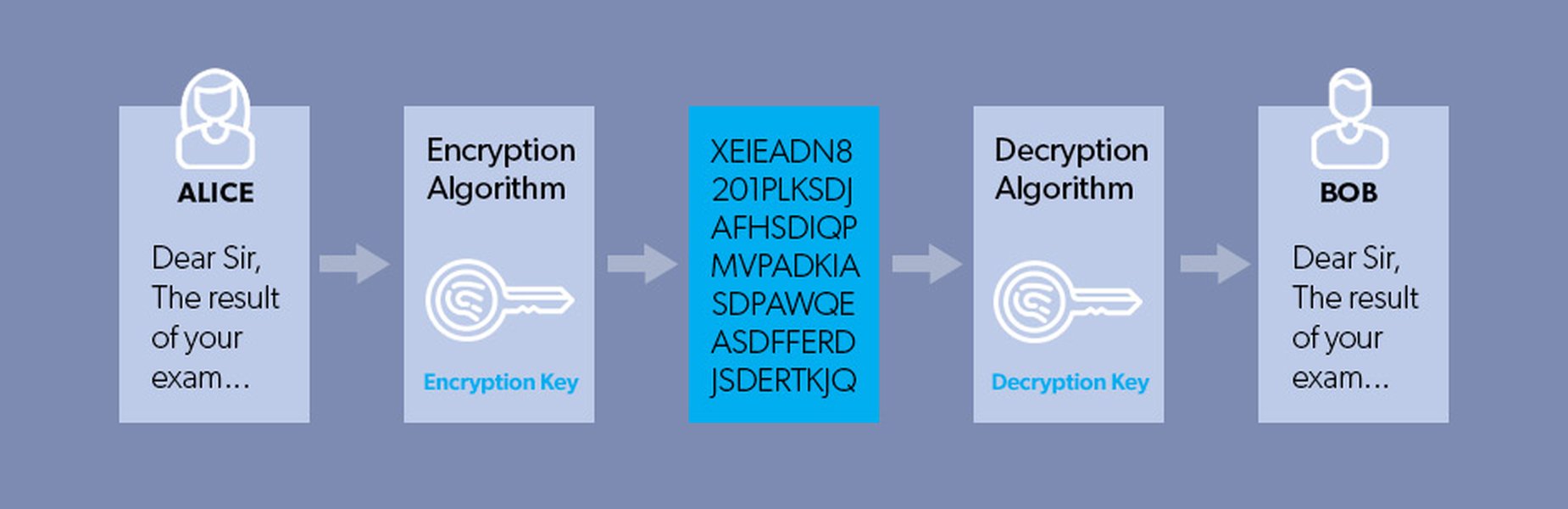
An illustration representing the concept of data encryption.
The Best Uses and Applications of Fully Homomorphic Encryption
Given its unique capabilities, FHE is poised to revolutionize various industries by enabling privacy-preserving data utilization. The "best" use case often depends on the specific context and the sensitivity of the data involved. However, several applications stand out due to the critical need for both computation and confidentiality.
Secure Cloud Computing and Storage
One of the most compelling use cases for FHE is in securing data stored and processed in the cloud. Organizations are increasingly leveraging cloud services for their scalability and cost-effectiveness, but concerns about data privacy and security in multi-tenant environments remain. FHE allows companies to outsource their data storage and processing to the cloud while ensuring that the cloud provider never has access to the unencrypted sensitive data. Computations can be performed on the encrypted data directly on the cloud servers, and the results are returned in encrypted form to the client for decryption. This dramatically decreases the likelihood of a security breach or data leak within the cloud infrastructure.
Privacy-Preserving Data Analytics
FHE is highly valuable for data analytics, especially in regulated industries such as healthcare, finance, and government. These sectors handle vast amounts of sensitive data that, if compromised, could have severe consequences. FHE enables organizations to perform complex statistical analyses, machine learning model training, and data mining on encrypted datasets without exposing the raw data. For example, healthcare researchers can collaborate on studies using patient data from multiple institutions without any party needing to share unencrypted patient records. Financial institutions can analyze encrypted transaction data to detect fraud or identify market trends without revealing individual customer details.
Visual representation of scaling Homomorphic Encryption for real-world applications.
Machine Learning on Encrypted Data
A particularly exciting application within data analytics is the ability to train and run machine learning models on encrypted data. This allows for privacy-preserving AI, where models can learn from sensitive datasets without ever seeing the plaintext. Researchers have demonstrated that it is possible to train machine learning models on fully encrypted banking data with similar accuracy to models trained on unencrypted data. This opens up possibilities for collaborative model training across organizations with sensitive data silos.
A video explaining machine learning over encrypted data using Fully Homomorphic Encryption.
This video delves into the practical application of FHE in the realm of machine learning. It highlights how FHE enables the training and execution of machine learning models on data that remains encrypted throughout the entire process. This is particularly relevant for scenarios involving sensitive datasets, where privacy regulations and concerns are paramount. The ability to perform complex computations like those involved in machine learning without decrypting the data is a significant step towards privacy-preserving AI and data analytics.
Enhancing Data Privacy in Various Domains
Beyond cloud and analytics, FHE has potential applications in numerous other areas where data privacy is critical:
Secure Elections
FHE can be used to enhance the security and privacy of electronic voting systems. It allows for computations on encrypted ballots to tally votes without ever revealing individual voters' choices, ensuring both accuracy and anonymity. Microsoft's ElectionGuard is an example of a system exploring the use of homomorphic encryption for this purpose.
Confidential Smart Contracts and Blockchain
In blockchain technology, FHE can be used to protect the confidentiality of transactions and the logic of smart contracts. This addresses the transparency issue in public blockchains where transaction details are typically visible to all participants. With FHE, computations within smart contracts can be performed on encrypted data, keeping sensitive information private while still leveraging the decentralized and immutable nature of the blockchain.
Privacy-Preserving Private Information Retrieval (PIR)
FHE can enable PIR, where a user can retrieve an item from a database without the database owner knowing which item was retrieved. The user sends an encrypted query, the server performs a homomorphic computation on the encrypted query and the database, and returns an encrypted result. The user can then decrypt the result to obtain the desired item without revealing their query to the server.
Secure Authentication and Biometrics
FHE can be used to process biometric data for authentication without exposing the raw biometric information. This can enhance the security of authentication systems by preventing the theft or misuse of sensitive biometric templates.
Challenges and the Future of FHE
Despite its immense potential, FHE is still a developing technology and faces certain challenges. One of the main hurdles has been performance. Early FHE schemes were computationally very expensive, making them impractical for many real-world applications. Performing operations on encrypted data can be significantly slower and require more computational resources compared to performing the same operations on plaintext data. However, ongoing research and advancements in algorithms and hardware are continuously improving the efficiency of FHE.

An illustration depicting the effort to make Fully Homomorphic Encryption a reality.
Another challenge is the complexity of implementing and working with FHE schemes. They require specialized knowledge and tools. However, the development of open-source libraries and frameworks is making FHE more accessible to developers.
The field of FHE is actively being researched, with continuous efforts to improve performance, develop more efficient algorithms, and explore new applications. As FHE becomes more practical and easier to use, its adoption is expected to grow significantly, transforming how we handle and process sensitive data in a privacy-preserving manner.
Comparison of Homomorphic Encryption Types
To summarize the different types of homomorphic encryption and their capabilities, the following table provides a comparison:
| Type | Supported Operations | Number of Operations | Complexity |
|---|---|---|---|
| Partially Homomorphic Encryption (PHE) | One type (either addition or multiplication) | Unlimited | Lower (compared to FHE) |
| Somewhat Homomorphic Encryption (SHE) | Both addition and multiplication | Limited | Medium |
| Leveled Fully Homomorphic Encryption (LHE) | Both addition and multiplication | Bounded (pre-determined depth) | Higher (compared to SHE) |
| Fully Homomorphic Encryption (FHE) | Both addition and multiplication | Unlimited | Highest (currently) |
Frequently Asked Questions about Fully Homomorphic Encryption
What is the main advantage of Fully Homomorphic Encryption over traditional encryption?
The primary advantage is the ability to perform computations directly on encrypted data without decrypting it. Traditional encryption requires decryption before processing, creating privacy vulnerabilities, whereas FHE maintains data confidentiality throughout the computation.
Is Fully Homomorphic Encryption currently used in real-world applications?
While still an area of active research and development, FHE is starting to be explored and implemented in various pilot programs and specific use cases, particularly in areas requiring high levels of data privacy like cloud computing and privacy-preserving analytics. Its widespread adoption is increasing as performance improves.
What are the biggest challenges facing the widespread adoption of FHE?
Historically, performance overhead (speed and computational resources required) and complexity of implementation have been major challenges. While significant progress has been made, further improvements are needed to make FHE more efficient and accessible for a broader range of applications.
How does FHE contribute to a zero-trust security model?
FHE supports a zero-trust model by ensuring that data remains encrypted even when being processed in potentially untrusted environments, like third-party cloud infrastructure. This minimizes the reliance on trusting the environment where the computation is performed.
Is FHE resistant to quantum computing attacks?
Many current FHE schemes are based on lattice-based cryptography, which is considered to be quantum-resistant. This makes FHE a promising technology for future-proofing data security against the threat of quantum computers that could break many of today's public-key cryptosystems.
References
Last updated April 29, 2025