
Mastering Configuration Management: Tools, Practices, and Strategic Advantages
Unlocking IT Consistency and Efficiency through Robust Configuration Strategies
Configuration Management (CM) is a critical discipline in IT and software engineering, focusing on establishing and maintaining consistency in a product's performance and functional attributes with its requirements, design, and operational considerations throughout its lifecycle. In today's complex and distributed IT environments, CM ensures system stability, reduces risks, and streamlines operations by systematically managing changes to hardware, software, and network configurations. It is fundamental for maintaining the integrity and traceability of IT systems and applications, providing a clear audit trail of changes, and ensuring compliance with industry regulations and security policies.
Key Insights into Configuration Management
- Consistency and Automation: Configuration management tools automate the process of setting up, deploying, and managing software and hardware configurations across diverse environments, ensuring uniformity and reducing manual errors.
- Leading Tools: Ansible, Chef, Puppet, and SaltStack are among the most prominent and widely adopted configuration management tools, each offering unique strengths in automation, scalability, and ease of use.
- Strategic Best Practices: Effective CM involves establishing a comprehensive Configuration Management Database (CMDB), adopting Infrastructure as Code (IaC), implementing automated enforcement of standards, and ensuring robust change control processes to enhance security, efficiency, and compliance.
Understanding Configuration Management
What is Configuration Management?
Configuration Management is a systems engineering process that tracks and controls changes to a software system, IT assets, and their configurations. It involves defining, documenting, and maintaining the desired state of IT systems and components. This process is crucial for system administrators and DevOps teams to keep track of the current state of applications and services, quickly identify systems that require attention, determine remediation steps, prioritize actions, and validate completion. By systematically managing configuration items (CIs), which can range from a piece of software to a server or a cluster of servers, CM helps prevent misconfigurations, enhances stability, and supports efficient troubleshooting.
The scope of configuration management has evolved significantly. Historically rooted in hardware development and production control in the 1950s, it later expanded to software development, addressing issues of schedule, budget, and quality. Today, CM is integral to DevOps practices, enabling automated, consistent, and reliable management of infrastructure and application configurations across different environments.
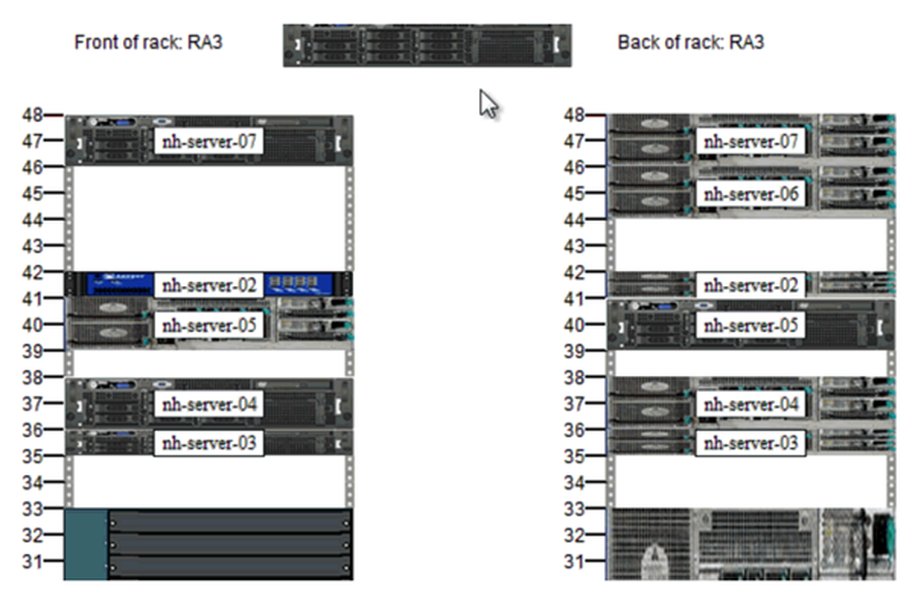
A well-organized server rack, a common target for configuration management.
Why is Configuration Management Important?
In modern IT landscapes, with increasing complexity, distributed systems, and rapid deployment cycles, configuration management is more critical than ever. It offers several significant benefits:
- Consistency and Predictability: CM ensures that applications behave predictably across development, testing, and production environments by enforcing consistent configurations.
- Automation: It automates repetitive tasks such as setting up servers, installing software, and configuring systems, significantly reducing manual effort and potential for human error.
- Change Control and Traceability: CM allows for controlled and documented changes to configuration items, providing an audit trail to identify who made what changes and why, enhancing traceability and accountability.
- Disaster Recovery and Rollback: By maintaining baselines and tracking changes, CM enables quick recovery from configuration issues and the ability to revert to previously stable configurations, preventing service disruption.
- Compliance and Security: Robust configuration management enhances compliance with industry regulations by providing a clear audit trail of configuration changes and consistent application of security policies across the entire IT infrastructure.
- Improved Collaboration: It provides a centralized platform for stakeholders to collaborate, share configurations, track changes, and resolve conflicts.
Leading Configuration Management Tools
The market offers a wide array of configuration management tools, each with distinct features and strengths. Selecting the right tool depends on organizational needs, infrastructure complexity, team skill sets, and scalability requirements. The following are some of the most widely used and influential tools:
Ansible
Ansible is an open-source automation engine that simplifies configuration management, application deployment, and orchestration. It is known for its simplicity and agentless architecture, meaning it doesn't require any special software to be installed on managed nodes. Ansible uses human-readable YAML syntax for its playbooks, making it accessible to users without extensive programming expertise. It operates on a "push" model, where a central server triggers updates to managed servers.
- Key Strengths: Easy to learn, agentless, human-readable YAML, strong community support, highly flexible for various use cases.
- Best for: Application deployment, orchestration, and simplified infrastructure automation.
Chef
Chef is a powerful automation platform that transforms infrastructure into code. It uses a Ruby-based Domain Specific Language (DSL) to define configuration policies. Chef operates on a "pull" model, where client nodes pull configurations from a central Chef server. It is particularly well-suited for complex environments and industries with strict regulatory requirements due to its robust capabilities for defining and enforcing desired states.
- Key Strengths: Infrastructure as Code (IaC) emphasis, strong for large-scale environments, robust policy enforcement, excellent for compliance.
- Best for: Infrastructure automation, especially in regulated industries and large enterprises.
Puppet
Puppet is another long-standing open-source configuration management tool that automates system administration tasks. Similar to Chef, it uses a declarative language (Puppet DSL) to define infrastructure as code and operates on a "pull" model. Puppet is highly scalable and offers strong reporting and auditing capabilities, making it a popular choice for managing thousands of nodes.
- Key Strengths: Mature and stable, strong reporting and auditing, large module ecosystem (Puppet Forge), ideal for consistent server configuration.
- Best for: Large-scale infrastructure management, enforcing desired state consistently.
SaltStack (Salt)
SaltStack is an open-source, Python-based configuration management system designed for high-speed data collection and execution. It uses a "master-minion" architecture and supports both push and pull models. SaltStack is known for its exceptional speed, scalability, and versatility, making it efficient for managing large-scale infrastructures and complex multi-cloud environments.
- Key Strengths: High-speed execution, scalable, versatile (supports push/pull), strong remote execution capabilities.
- Best for: Real-time infrastructure management, rapid configuration changes, multi-cloud setups.
Other Notable Tools
- Terraform: Primarily an Infrastructure as Code (IaC) tool for provisioning and managing cloud and on-premises infrastructure resources, often used alongside configuration management tools for a complete solution.
- Docker: While not a traditional configuration management tool, Docker containers encapsulate applications and their dependencies, providing a consistent environment across development and production.
- CFEngine: One of the older open-source configuration management tools, known for its stability and efficiency in managing huge computer systems.
- PowerShell DSC: Microsoft's Desired State Configuration (DSC) for Windows environments, allowing IT professionals to manage configuration through code.
Comparative Analysis of Configuration Management Tools
To provide a clearer perspective on the strengths of the discussed tools, the following radar chart illustrates their typical performance and characteristics across several key attributes. These values are based on general industry perception and common use cases rather than specific benchmarks, offering a qualitative comparison to guide tool selection.
Qualitative Comparison of Leading Configuration Management Tools
This radar chart highlights the perceived strengths of each tool. Ansible shines in ease of learning and flexibility due to its agentless nature and YAML syntax. Chef and Puppet are strong in scalability and automation power, particularly for complex infrastructure and environments requiring strict compliance. SaltStack is notable for its exceptional speed and versatility, making it a strong contender for dynamic and large-scale infrastructures. The "Security Focus" dimension considers how well a tool inherently supports security best practices through its design and features, such as policy enforcement and auditing capabilities.
Configuration Management Best Practices
Implementing configuration management effectively requires adherence to best practices to maximize its benefits and mitigate risks. These practices ensure consistency, enhance security, and streamline operations in increasingly distributed and complex IT environments.
Strategic Implementation Guidelines
-
Establish a Comprehensive Configuration Management Database (CMDB)
A CMDB serves as the centralized repository for all configuration items (CIs) and their relationships. It provides a holistic view of the IT landscape, enabling better decision-making, impact analysis, and troubleshooting. The CMDB should be regularly updated and verified to ensure accuracy. This is the foundation for effective CM, allowing organizations to track and manage changes to CIs, from hardware and software to network settings.
-
Automate Configuration Enforcement
Leverage configuration management tools to automate the enforcement of configuration standards and policies. Automated enforcement ensures consistency across systems, reduces human error, and improves compliance. This practice shifts from manual, reactive fixes to proactive, automated maintenance of desired states.
-
Adopt Infrastructure as Code (IaC)
Treat infrastructure configurations as code. This means defining, versioning, testing, and deploying infrastructure using the same principles and tools as software development. IaC promotes consistency, reproducibility, and traceability of infrastructure changes, allowing for rapid and reliable deployments. Tools like Terraform and Ansible play a crucial role here, enabling declarative definitions of infrastructure.
-
Implement Robust Change Control and Versioning
All changes to configurations should be managed through a controlled process, including review, approval, and documentation. Use version control systems (like Git) for configuration files to track changes, enable rollbacks, and provide a clear history of modifications. This ensures that changes are introduced in a controlled manner, minimizing unexpected problems.
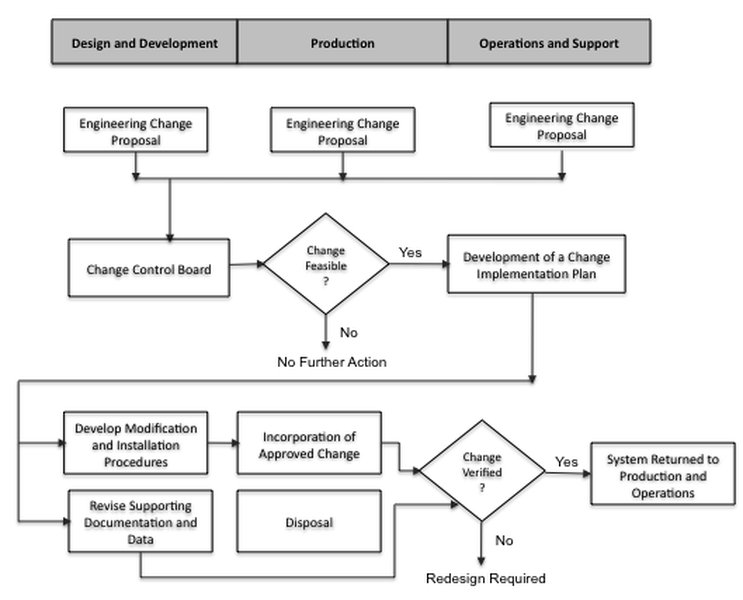
Standard Change Control Process in Configuration Management.
-
Define and Document Processes
Clearly define and document your configuration management processes, including roles, responsibilities, and activities. Align these processes with industry best practices frameworks such as ITIL, COBIT, or ISO20000 to ensure consistency and efficiency. Comprehensive documentation is vital for training personnel, maintaining process adherence, and ensuring a clear audit trail.
-
Gradual Deployment and Rollbacks
Avoid global "all-at-once" pushes of new configurations. Instead, deploy new configurations gradually (e.g., in phases or to a subset of systems first) to identify and address issues before they impact the entire environment. Always have a clear incident management process and rollback plan in place to quickly address and revert problematic configurations.
-
Regular Auditing and Monitoring
Continuously monitor configuration states and conduct regular audits to ensure compliance with defined baselines and policies. Automated monitoring tools can detect deviations from the desired state, alerting teams to potential misconfigurations or security vulnerabilities. This proactive approach helps maintain system integrity and security posture.
The Role of Configuration Management in DevOps and CI/CD
Configuration Management is a cornerstone of modern DevOps practices and Continuous Integration/Continuous Delivery (CI/CD) pipelines. It provides the necessary automation and consistency to support the rapid and reliable deployment of software across various environments.
This video provides a detailed overview of configuration management, its importance, how it works in software development and IT, best practices, and challenges.
In a CI/CD pipeline, configuration management tools manage configurations for development, testing, and production environments, ensuring that the software works consistently across all stages. By codifying configurations and integrating them into version control, teams can apply the same rigorous quality standards to configuration files as they do to application code. This approach, often referred to as "Configuration-as-Code (CaC)," emphasizes managing configurations with the same discipline as software code, enhancing visibility, consistency, and quality of deployed software.
The automation provided by CM tools within CI/CD pipelines cuts down on repetitive tasks for setting up, deploying, and managing software configurations. This leads to accelerated software delivery, reduced manual errors, and improved overall system reliability.
Challenges and Considerations
Despite its numerous benefits, implementing and maintaining configuration management can present challenges:
| Challenge Area | Description | Mitigation Strategy |
|---|---|---|
| Complexity of Data | The sheer volume and diversity of configuration data can be overwhelming, leading to difficulties in tracking and managing CIs effectively. | Prioritize critical CIs, implement a robust CMDB, and automate data collection and updates. |
| Integration Issues | Integrating CM tools with existing IT systems (e.g., ITSM, monitoring, security tools) can be complex and require significant effort. | Choose tools with open APIs and strong integration capabilities. Plan integration points early in the implementation phase. |
| Skill Gap | Teams may lack the necessary skills to effectively use and manage configuration management tools and implement best practices. | Invest in continuous training and upskilling for IT and DevOps teams. Foster a culture of learning and collaboration. |
| Resistance to Change | Shifting from manual processes to automated configuration management can face resistance from team members accustomed to traditional methods. | Communicate the benefits clearly, involve stakeholders early, provide adequate training, and demonstrate quick wins. |
| Maintaining Baselines | Establishing and continuously maintaining accurate baselines for configurations, especially in dynamic environments, can be challenging. | Automate baseline creation and verification. Implement continuous monitoring to detect and remediate deviations promptly. |
Overcoming these challenges requires careful planning, adequate resources, and a commitment to continuous improvement. Organizations should approach CM as an ongoing process, adapting strategies and tools as their IT landscape evolves.
Frequently Asked Questions (FAQ)
Conclusion
Configuration Management is an indispensable discipline for any organization aiming to achieve consistent, reliable, and secure IT operations. By adopting leading tools like Ansible, Chef, Puppet, and SaltStack, and diligently implementing best practices such as Infrastructure as Code, automated enforcement, and robust change control, businesses can significantly enhance their agility, reduce operational risks, and maintain compliance in an ever-evolving digital landscape. The strategic application of CM not only streamlines IT workflows but also empowers DevOps teams to deliver software more efficiently and with greater confidence.
Recommended Further Exploration
- Deep dive into Infrastructure as Code (IaC) principles and tools
- Advanced DevOps automation strategies with configuration management
- Integrating Configuration Management with CI/CD pipelines for seamless deployments
- Best practices for securing configurations in cloud environments
References
Last updated May 21, 2025