
Unveiling Digital Risk Protection: Safeguarding Your Enterprise in a Hyper-Connected World
Proactive strategies to defend against external digital threats and fortify your brand's integrity.
In today's rapidly evolving digital landscape, organizations face an expanding array of external threats that lie beyond traditional IT perimeters. Digital Risk Protection (DRP) has emerged as a critical cybersecurity discipline, offering a proactive and comprehensive approach to safeguarding an organization's digital assets, brand reputation, and key personnel from sophisticated external cyber threats. Unlike conventional security measures that primarily focus on internal networks, DRP extends its vigilance across the vast expanse of the public internet, deep web, and dark web, identifying and mitigating risks before they can escalate into costly breaches or reputational damage.
Essential Insights into Digital Risk Protection
- DRP is a proactive cybersecurity discipline that monitors and mitigates threats originating outside an organization's internal IT environment, such as brand impersonation, data leaks, and targeted attacks across the open, deep, and dark web.
- Comprehensive protection extends beyond traditional security to cover a wide spectrum of external digital risks, including sophisticated AI-driven threats and supply chain vulnerabilities.
- Effective DRP solutions integrate cutting-edge technology like AI and neural networks with human expertise for continuous monitoring, accurate threat detection, rapid response, and seamless integration with existing security frameworks.
What is Digital Risk Protection (DRP)?
Digital Risk Protection (DRP) represents a crucial evolution in cybersecurity, shifting the focus from reactive defense to proactive identification and neutralization of external threats. It encompasses a suite of technologies and services designed to continuously monitor, identify, assess, and mitigate risks that originate from an organization's digital footprint across the internet's vast landscape. This includes public websites, social media platforms, business collaboration tools, app stores, and the more clandestine realms of the deep and dark web.
DRP goes beyond traditional perimeter security by actively looking for threats where attackers operate and where compromised data often surfaces. It acts as an early warning system, utilizing intelligent algorithms and various reconnaissance methods to find, track, and analyze threats in real-time. This proactive stance is essential for protecting not only digital assets but also the invaluable brand reputation and the safety of executives and employees.
Why is DRP Important?
The importance of DRP has never been more pronounced than in today's interconnected business world. Digital transformation, characterized by increased cloud adoption, hybrid work models, and reliance on third-party vendors, has exponentially expanded organizations' attack surfaces. This expansion creates numerous new entry points for threat actors, making traditional internal-focused security insufficient. Furthermore, the rapid advancement and accessibility of AI technologies empower attackers to automate and enhance their campaigns, from crafting hyper-realistic deepfakes to generating convincing phishing content, making it increasingly difficult for security teams to keep pace.
DRP is crucial because it helps organizations:
- Prevent Costly Breaches: By detecting and mitigating threats like data leaks and phishing campaigns before they escalate, DRP helps prevent financial losses, legal repercussions, and severe reputational damage.
- Reduce Financial and Reputational Harm: Proactive identification of brand impersonation and fraudulent activities minimizes the negative impact on customer trust and market standing.
- Strengthen Overall Cybersecurity Posture: DRP complements existing security frameworks by providing external visibility, transforming cybersecurity strategies from reactive incident response to proactive threat prevention.
- Ensure Business Continuity: Protecting new systems and technologies as they integrate into the digital ecosystem helps maintain operational stability and functionality.
The global DRP market is projected to grow significantly, underscoring its essential role in modern corporate cybersecurity strategies as businesses navigate an increasingly hostile digital environment.
What Does DRP Protect You From?
DRP offers comprehensive protection against a wide spectrum of external digital threats that can originate outside an organization’s internal IT environment. These threats exploit various digital channels to achieve malicious aims:
-
Brand Impersonation
This category involves the misuse of an organization's brand identity to deceive customers or partners, often with the goal of committing fraud or damaging reputation. DRP continuously monitors for and detects:
- Fake Domains and Websites: Identification of fraudulent websites designed to mimic legitimate ones, used for phishing, distributing malware, or selling counterfeit goods.
- Social Media Impersonators: Detection of unauthorized social media accounts, profiles, or pages that pose as the organization or its executives to spread misinformation, conduct scams, or solicit sensitive information.
- Rogue Mobile Applications: Discovery of malicious apps in unofficial app stores or third-party sites that impersonate legitimate organizational apps, often containing malware or designed for credential theft.
- Counterfeit Product Listings: Alerts on online marketplaces and e-commerce sites where counterfeit versions of an organization’s products are being sold, damaging brand integrity and revenue.
By identifying these impersonations early, DRP enables rapid takedown actions, preserving brand trust and preventing customer exploitation.
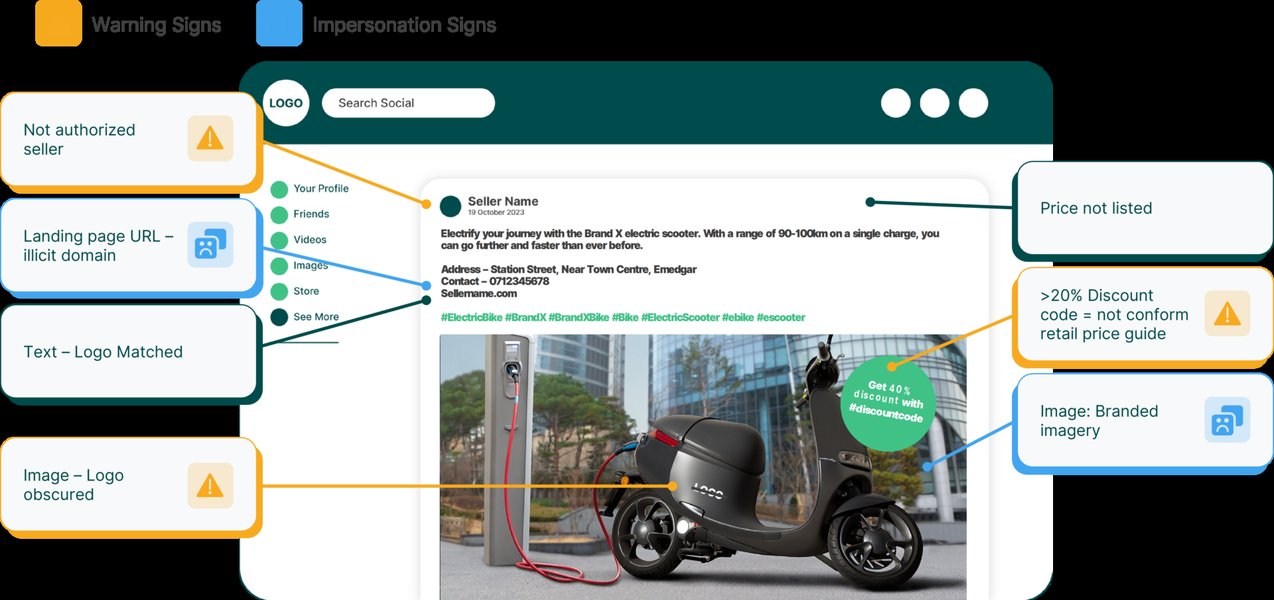
An illustrative example of a brand impersonation profile discovered through digital risk monitoring.
-
Data Leaks and Dark Web Exposure
DRP continuously monitors criminal forums, underground marketplaces, and other dark web sources to detect the exposure of sensitive data. This includes:
- Compromised Credentials: Identification of leaked employee or customer usernames, passwords, and other authentication details that could lead to account takeovers.
- Personally Identifiable Information (PII): Detection of exposed personal data such as names, addresses, social security numbers, and financial information that can be used for identity theft or targeted attacks.
- Intellectual Property and Trade Secrets: Discovery of proprietary code, confidential documents, designs, or research being shared or sold illicitly.
- Financial and Corporate Data: Alerts on the leakage of sensitive financial records, corporate strategies, or internal communications.
Visibility into these exposures allows organizations to take immediate action, such as forced password resets or data recovery efforts, to prevent further exploitation.
-
Phishing and Scam Campaigns
DRP solutions actively identify and disrupt the infrastructure used for phishing and scam campaigns targeting employees, customers, or partners. This involves:
- Phishing Site Detection: Identifying and flagging fraudulent domains and websites designed to trick users into divulging credentials or installing malware.
- Malicious Posts and Messages: Monitoring social media, email, and messaging platforms for active scam attempts, spear-phishing campaigns, or links to malicious content.
- Ransomware and Malware Distribution: Detecting external sources attempting to distribute malware or initiate ransomware attacks, often disguised as legitimate software or links.
By disrupting these campaigns early, DRP prevents successful cyberattacks and protects individuals from falling victim to scams.
-
Executive and Employee Targeting
High-profile individuals within an organization are often prime targets for sophisticated attacks. DRP offers specialized protection against:
- Spear Phishing and Business Email Compromise (BEC): Detecting highly personalized phishing attempts aimed at executives or key employees, often leveraging leaked personal information to trick them into unauthorized actions or financial transfers.
- Deepfake Impersonations: Identifying AI-generated voice or video impersonations used in highly convincing social engineering attacks.
- Personal Information Leaks: Monitoring for personal data of executives and employees exposed on the dark web or public forums that could be leveraged for social engineering or physical threats.
- Executive Impersonation: Detecting instances where attackers impersonate executives on social media or other platforms to spread false information or demand sensitive data from employees.
-
Emerging and Supply Chain Risks
DRP extends its protective scope to cover a broader range of digital threats, including:
- Supply Chain Vulnerabilities: Identifying risks originating from third-party vendors and partners whose compromised digital exposure could impact the organization.
- Shadow IT Assets: Detecting unauthorized IT assets or services used within the organization that are exposed externally and pose security risks.
- Disinformation Campaigns: Monitoring for coordinated efforts to spread false or misleading information about the organization, its products, or leadership, which can severely impact reputation.
- Code Leakage: Identifying instances where proprietary source code or development credentials are leaked on public code repositories or developer forums.
By addressing these multifaceted threats, DRP provides a holistic shield, ensuring no blind spots in an organization's external digital ecosystem.
How Does Digital Risk Monitoring Work?
Digital risk monitoring, the operational backbone of DRP, is a continuous, automated process that leverages advanced technology and human expertise to scan and analyze vast amounts of digital data. The process typically involves several key steps:
-
Digital Footprint Mapping
The initial phase involves identifying and cataloging all digital assets associated with an organization. This includes websites, domain names, social media accounts, mobile applications, cloud instances, and any other internet-facing assets. This mapping provides a comprehensive understanding of the organization's external attack surface.
-
Continuous Data Collection and Scanning
DRP platforms continuously scan diverse digital channels for signs of threats. This includes:
- Open Web: Publicly accessible websites, news sites, blogs, and forums.
- Social Media: Popular platforms like Facebook, X (formerly Twitter), LinkedIn, Instagram, and more, monitoring for mentions, impersonations, and malicious content.
- Deep Web: Content not indexed by standard search engines, such as databases and password-protected forums, accessed via specialized APIs.
- Dark Web: Hidden networks (e.g., Tor) used for illicit activities, including criminal forums, underground marketplaces, and paste sites where compromised data often surfaces.
- App Stores: Official and unofficial mobile application stores to detect rogue or malicious apps impersonating the brand.
- Business Collaboration Tools: Monitoring for data leaks or unauthorized discussions in platforms like Slack or Microsoft Teams that might be publicly exposed.
-
AI-Driven Analysis and Threat Intelligence Integration
Once data is collected, DRP software employs AI, machine learning, and neural networks to filter, analyze, and prioritize potential threats. This intelligent analysis helps distinguish genuine threats ("signal") from irrelevant information ("noise"). DRP solutions integrate with cyber threat intelligence (CTI) feeds, which provide context on active threat actors, their tactics, techniques, and procedures (TTPs), and emerging indicators of compromise (IOCs). This integration enhances the platform's ability to identify relevant risks and provide early warnings.
-
Contextual Enrichment and Human Curation
While automation is key, human expertise remains vital. Security analysts review high-priority alerts, add context, and verify the legitimacy of threats. This human curation ensures accuracy, minimizes false positives, and provides nuanced insights for effective response planning.
-
Alerting and Response Integration
When a risk is detected, DRP platforms generate context-rich alerts, often with clear response steps and mitigation recommendations. These alerts are often integrated seamlessly with existing security infrastructure, such as Security Information and Event Management (SIEM) systems and Security Orchestration, Automation, and Response (SOAR) platforms. This integration allows external risk insights to feed directly into internal security operations, enabling swift and coordinated incident response.
An illustration of the workflow for Digital Risk Monitoring, highlighting its key stages from mapping to response.
Core Capabilities of a DRP Solution
An effective Digital Risk Protection solution provides a robust set of capabilities designed to offer comprehensive visibility and proactive mitigation against external threats. These core functionalities ensure that organizations can effectively monitor, detect, and respond to risks across their entire digital footprint:
-
Comprehensive Coverage and Visibility
A top-tier DRP platform offers extensive monitoring across all relevant digital channels, including the clear web, deep web, dark web, social media platforms, app stores, and business collaboration tools. This ensures that all exposed assets and potential attack surfaces are continuously under surveillance, leaving no blind spots.
-
Real-time Threat Detection and Alerting
DRP solutions provide continuous, automated monitoring with the ability to detect anomalies and potential threats in real time. This includes identifying brand impersonations, data leaks, phishing sites, and targeted attacks as they emerge, allowing for rapid response. Alerts are context-rich and often prioritized based on criticality.
-
Incident Response & Takedown Services
Beyond detection, effective DRP platforms offer proactive mitigation capabilities. This includes the ability to disrupt cyber attack infrastructure, initiate takedown requests for malicious domains, phishing kits, fake social media profiles, and counterfeit product listings before they can cause significant harm.
-
Brand Protection and Monitoring
A core function is to monitor brand mentions, identify instances of brand impersonation, infringement, and fraudulent use. This helps prevent brand abuse, protect intellectual property, and safeguard customer trust.
-
Credential Leak Detection
DRP continuously scans underground forums and dark web marketplaces for compromised employee and customer credentials. Early identification of leaked data allows organizations to force password resets and prevent unauthorized access or account takeovers.
-
Advanced Analytics and Prioritization
Leveraging machine learning and AI, DRP solutions provide sophisticated analytics to filter out noise, reduce false positives, and prioritize threats based on their potential impact. This helps security teams focus on the most critical risks and optimize their response efforts.
-
Integration Capabilities
Seamless integration with existing cybersecurity infrastructure is vital. DRP platforms should connect effortlessly with Security Information and Event Management (SIEM) systems, Security Orchestration, Automation, and Response (SOAR) platforms, and Cyber Threat Intelligence (CTI) tools to streamline workflows and provide a holistic security posture.
-
Scalability and Customization
A robust DRP solution should be scalable to accommodate an organization's evolving digital footprint across various geographies and sectors. It should also offer customization options for tailored threat models that reflect unique organizational risks and compliance requirements.
-
Executive and High-Profile Employee Protection
Many DRP solutions offer specialized monitoring for VIPs and high-profile employees, protecting them from targeted attacks, impersonation attempts, and personal information leaks that could be leveraged for social engineering or other malicious activities.
This radar chart compares the perceived performance of an ideal DRP platform against a typical DRP platform across various core capabilities. The data points, ranging from 5.5 to 9.8, represent an assessment of how well platforms generally execute each function. An ideal DRP solution excels in areas like real-time detection and brand protection, while a typical platform may show variability in takedown capabilities or executive protection. This visual helps in understanding the desired benchmarks for a robust DRP implementation.
Real-World Use Cases for DRP
Digital Risk Protection provides tangible benefits across various industries by addressing specific external digital threats:
-
Financial Institutions
DRP is crucial for preventing fraud, protecting sensitive financial data, and maintaining regulatory compliance. It helps detect phishing domains impersonating banks, identify leaked customer banking credentials on the dark web, and monitor for fraudulent investment schemes that misuse financial brand names.
-
Healthcare Providers
Safeguarding patient data and ensuring HIPAA compliance are paramount. DRP monitors for exposed patient records, misconfigured cloud storage that could leak sensitive health information, and spear-phishing campaigns targeting healthcare professionals to gain access to medical systems.
-
Retail Businesses
DRP protects brand reputation and ensures customer safety. It identifies counterfeit product listings on e-commerce platforms, detects fake social media accounts running fraudulent promotions, and monitors for credit card data dumps on underground forums linked to past breaches.
-
Technology Companies
Essential for protecting intellectual property and combating software piracy. DRP helps identify code leakage on public repositories, detect compromised developer credentials, and uncover pirated software being distributed through illicit channels.
-
Government Organizations
DRP aids in mitigating risks from deep and dark web leakages, targeted espionage campaigns, and disinformation efforts that could undermine public trust or national security.
-
Manufacturing and Industrial Sectors
DRP can protect against intellectual property theft related to designs and processes, identify supply chain vulnerabilities, and detect industrial espionage attempts originating from external digital channels.
This video from FortiRecon showcases their Brand Protection capabilities as part of their Digital Risk Protection (DRP) service. It illustrates how DRP continuously monitors an organization's digital footprint to identify and mitigate threats related to brand impersonation and digital fraud. This directly relates to a critical use case of DRP: safeguarding brand integrity across various online channels, a constant challenge for businesses today.
What to Look For in a DRP Platform
Selecting the right DRP platform is crucial for maximizing its effectiveness. When evaluating solutions, consider the following critical factors:
| Criterion | Description | Key Considerations |
|---|---|---|
| Coverage: Where and What It Monitors | The breadth and depth of digital channels the platform monitors. | Does it cover the open web, deep web, dark web, social media, app stores, and business collaboration tools? Does it monitor for brand mentions, credential leaks, phishing infrastructure, and executive impersonations? Comprehensive coverage is key to eliminating blind spots. |
| Accuracy: Signal vs. Noise | The platform's ability to distinguish genuine threats from irrelevant information or false positives. | Look for solutions that leverage advanced AI, machine learning, and neural networks to reduce alert fatigue. A high signal-to-noise ratio ensures that security teams receive actionable intelligence, not just overwhelming data. |
| Response: How Fast and How Far It Goes | The speed of threat detection, alerting, and the platform's capabilities for mitigation and remediation. | Evaluate the platform's ability to provide real-time alerts. Does it offer automated takedown services for malicious domains or fake profiles? Is there expert support for complex mitigation efforts? Rapid and comprehensive response is essential for minimizing damage. |
| Integration: With SIEM, SOAR, Threat Intel Tools | The platform's compatibility and seamless integration with existing cybersecurity infrastructure. | Can it feed alerts and intelligence directly into your SIEM for centralized logging and correlation? Does it integrate with SOAR platforms for automated incident response workflows? Interoperability with threat intelligence tools enhances context and informs strategic defenses. |
| User Experience and Reporting | The clarity, intuitiveness, and reporting capabilities of the platform's interface. | Are dashboards customizable? Are alerts clear and easy to understand? Does it offer comprehensive reporting on threat trends, mitigation efforts, and the overall ROI of your security investment? |
| Scalability and Customization | The platform's ability to grow with your organization's needs and adapt to unique risks. | Can it scale to protect a growing digital footprint across different geographies and business units? Does it allow for customized threat models and monitoring rules to address specific industry or organizational risks? |
Key criteria for evaluating and selecting an optimal Digital Risk Protection platform.
Who Needs DRP?
In today's dynamic digital ecosystem, DRP has become a necessity for organizations of all sizes, particularly those with a significant online presence or handling sensitive data. It is highly beneficial for various industries and specific roles within an organization:
-
Use Cases by Industry
- Finance: Essential for fraud prevention, protecting against phishing attacks targeting customers, safeguarding sensitive financial transactions, and ensuring compliance with stringent financial regulations.
- Healthcare: Critical for protecting patient data (PHI), ensuring compliance with regulations like HIPAA, and monitoring for data leaks of medical records or targeted attacks on healthcare infrastructure.
- Retail: Paramount for protecting brand reputation, combating counterfeit product sales, preventing online fraud, and safeguarding customer data during online transactions.
- Technology: Vital for protecting intellectual property, combating software piracy, securing proprietary code, and defending against sophisticated attacks targeting R&D or product development.
- Manufacturing: Important for protecting industrial designs, supply chain integrity, and intellectual property from espionage or unauthorized sharing.
- Government & Public Sector: Crucial for mitigating disinformation campaigns, protecting sensitive government data, and defending against state-sponsored cyber threats.
- Telecommunications: Necessary for protecting customer data, preventing service disruption due to external attacks, and securing digital infrastructure.
-
Ideal for Specific Roles
- Security Operations Center (SOC) Teams: DRP provides external threat intelligence and actionable alerts, enabling SOC teams to proactively monitor and respond to emerging risks beyond their internal network.
- Risk Management Officers: DRP offers crucial visibility into external risks that could impact business continuity, financial stability, and regulatory compliance, allowing for more informed risk assessments and mitigation strategies.
- Brand Protection Leads & Marketing Teams: These professionals benefit immensely from DRP's ability to detect brand impersonation, copyright infringement, and malicious social media activity, enabling them to protect brand value and customer trust.
- Compliance Teams: DRP helps identify and address exposures of sensitive data that could lead to regulatory non-compliance (e.g., GDPR, CCPA), ensuring that organizations meet their legal obligations.
- Executive Security Teams: DRP provides specialized protection for high-profile individuals, guarding against targeted attacks like deepfake scams and personal information leaks that could be used for social engineering.
DRP vs. EASM vs. Threat Intelligence: A Quick Breakdown
While Digital Risk Protection (DRP), External Attack Surface Management (EASM), and Threat Intelligence (TI) all focus on external cybersecurity, they have distinct primary objectives and methodologies, though they are often complementary:
-
Digital Risk Protection (DRP)
Focus: Primarily on identifying and mitigating *external threats* that originate from an organization's digital footprint beyond its internal IT environment. Its core aim is to protect brand reputation, digital assets, and high-profile individuals from threats like brand impersonation, data leaks, phishing, and executive targeting across public, deep, and dark web channels. DRP is proactive, aiming to disrupt attacks before they materialize into breaches.
Example: Detecting a fake domain impersonating your company's login page on the clear web, or identifying compromised employee credentials being sold on a dark web forum.
-
External Attack Surface Management (EASM)
Focus: Discovering and managing *all internet-facing assets* that an organization owns or is associated with. The goal is to gain a comprehensive understanding of the external attack surface to identify vulnerabilities (e.g., misconfigured servers, outdated software, open ports) that attackers could exploit. EASM is about mapping and inventorying the external digital perimeter.
Example: Discovering an unpatched web server exposed to the internet that your IT team was unaware of, or identifying an abandoned subdomain that could be hijacked.
-
Threat Intelligence (TI)
Focus: The collection, analysis, and dissemination of *information about potential or existing threats* that could harm an organization. This includes data on threat actors, their tactics, techniques, and procedures (TTPs), and malicious indicators (IOCs) such as IP addresses, domains, or file hashes. TI provides context and early warnings to inform security strategies and improve incident response.
Example: Receiving a report about a new ransomware family targeting your industry, or learning about a specific threat actor group's recent campaigns and their preferred attack vectors.
Key Differences & Overlaps:
- DRP vs. EASM: While both focus on external aspects, EASM is foundational, providing the map of the external digital assets and their vulnerabilities. DRP then actively monitors those assets and the broader external environment for active threats and malicious activities. EASM informs DRP by defining the scope of what needs protection.
- DRP vs. Threat Intelligence: DRP solutions often incorporate threat intelligence as a core capability to provide early warning of threats and emerging risks. However, TI is broader, offering analytical insights into the threat landscape, whereas DRP specifically applies that intelligence to proactively monitor and mitigate risks to an organization's brand, data, and personnel.
In essence, EASM provides the map of the external attack surface, Threat Intelligence provides the knowledge about who might attack and how, and DRP actively monitors and mitigates threats on that surface using the intelligence gathered. They are complementary disciplines that, when combined, offer a robust external cybersecurity defense.
Frequently Asked Questions (FAQ)
Conclusion
As the digital landscape continues to expand and evolve, so do the sophisticated threats that target organizations from beyond their traditional boundaries. Digital Risk Protection (DRP) has emerged as an indispensable component of a comprehensive cybersecurity strategy, providing the necessary visibility and proactive measures to safeguard an organization's brand, data, and people from external risks. By continuously monitoring the vast expanse of the internet—from public platforms to the clandestine dark web—DRP empowers businesses to detect, analyze, and mitigate threats such as brand impersonation, data leaks, and targeted attacks before they can inflict significant damage. Investing in a robust DRP solution is no longer merely an option but a critical imperative for maintaining trust, ensuring business continuity, and preserving integrity in our hyper-connected world.
Recommended Queries for Deeper Insights
- How AI-driven deepfakes impact digital risk protection strategies
- Best practices for integrating DRP with existing security operations
- Regulatory compliance implications for digital risk protection
- The role of human intelligence in modern DRP solutions