
Fortifying Your DigitalOcean Droplets: A Dual Perspective on Provisioning and Hardening
Unlocking advanced server security through strategic setup and rigorous defense, informed by ethical hacking and cybersecurity expertise.
Key Security Highlights
- Proactive Security Integration: Server provisioning on DigitalOcean must embed security from the ground up, leveraging API-driven automation and Cloud-Init to deploy hardened configurations and enforce SSH key-based authentication, minimizing initial attack surfaces.
- Comprehensive Hardening Layers: Beyond initial setup, continuous server hardening involves meticulous OS updates, removal of unnecessary components, strict access controls (least privilege, MFA), robust firewall rules (DigitalOcean Cloud Firewalls, VPC), and application-level security, aligning with industry benchmarks like CIS.
- Ethical Hacker's Mindset for Resilience: A cybersecurity professional adopts an ethical hacker's perspective to continuously test and validate these security measures through reconnaissance, vulnerability scanning, and simulated attack scenarios, ensuring that defenses are not only implemented but are also effective against evolving threats.
Understanding Server Provisioning on DigitalOcean: A Security Foundation
Laying the Secure Groundwork for Your Cloud Infrastructure
Server provisioning on DigitalOcean, where virtual machines are known as "Droplets," is the initial phase of deploying your cloud infrastructure. For an ethical hacker and cybersecurity professional, this stage is not merely about setting up a server; it's about embedding security from the very first step. Improper provisioning can introduce significant vulnerabilities, making the server an easy target for malicious actors.
Strategic Droplet Selection and Isolation
Choosing the right Droplet plan is fundamental, as it dictates the resources available and influences the attack surface. Over-provisioning can introduce unnecessary complexity, while under-provisioning might lead to performance issues that could indirectly impact security. Furthermore, isolating different workloads into separate DigitalOcean projects or environments, often utilizing Virtual Private Cloud (VPC) features, is crucial. This segmentation limits lateral movement within your network if a breach occurs in one segment.
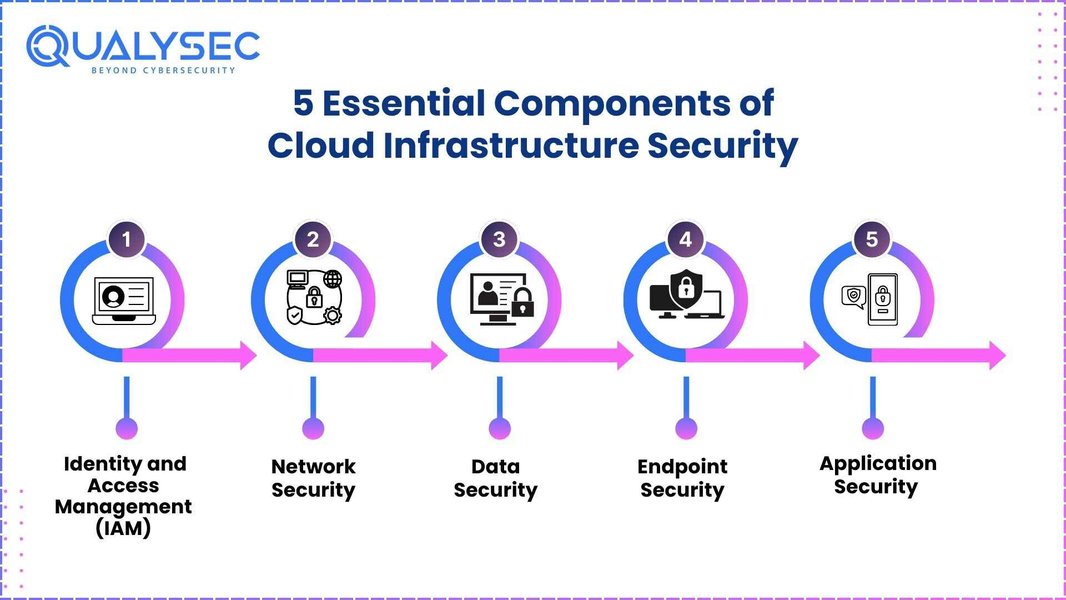
Illustrating essential components of cloud infrastructure security.
Automated and Secure Provisioning with Cloud-Init and APIs
DigitalOcean's robust API enables automated provisioning, which is highly recommended for consistency and reducing human error. Tools like Ansible or custom scripts can leverage this API to deploy Droplets with predefined, secure configurations. A cornerstone of secure provisioning is the use of SSH key-based authentication instead of passwords. DigitalOcean, by default, disables password authentication when SSH keys are provided, significantly mitigating brute-force attack risks.
Cloud-Init, supported by DigitalOcean, is an invaluable tool for ethical hackers and cybersecurity professionals. It allows for the execution of user data scripts upon a Droplet's first boot. This capability is used to:
- Install essential security tools.
- Apply immediate OS updates and patches.
- Configure initial firewall rules.
- Disable unnecessary services.
This proactive approach ensures that the server starts in a hardened state, preventing it from being exposed with default, vulnerable settings.
Network Configuration at Provisioning
During provisioning, meticulous network configuration is vital. Restricting open ports to only what is absolutely necessary (e.g., SSH on port 22, HTTP/HTTPS on 80/443 for web servers) minimizes the exposed attack surface. Leveraging DigitalOcean's cloud firewalls at the project or Droplet level to control inbound and outbound traffic is a critical initial defense layer. For sensitive systems, implementing Virtual Private Clouds (VPC) or private networking further segregates traffic, preventing public exposure of management interfaces.
Deep Dive into Server Hardening: A Proactive Defense Strategy
Strengthening Your DigitalOcean Droplets Against Cyber Threats
Server hardening is a continuous, systematic process of enhancing security measures to reduce vulnerabilities and mitigate risks of exploitation. From a cybersecurity perspective, this is a proactive defense that increases the "cost of entry" for attackers, making it significantly harder for them to gain unauthorized access or exploit system weaknesses.
Operating System Hardening: The Core Foundation
The operating system (OS) is the bedrock of your server, and its hardening is paramount. This involves:
- Regular Updates and Patching: Immediately applying OS security updates and patches after provisioning is non-negotiable. Unpatched systems are the easiest targets for attackers, often exploited using known vulnerabilities.
- Minimizing Attack Surface: Every installed package, utility, and running service introduces potential vulnerabilities. Removing or disabling non-essential software, services, and accounts significantly reduces the attack surface.
- Strict File System Permissions: Implementing appropriate file and directory access controls is crucial. This includes securing critical configuration files (e.g.,
/etc/ssh/sshd_config), log files, and user directories to prevent unauthorized modifications. - User Account and Privilege Management: Enforcing strong password policies, limiting user account creation, and adhering to the Principle of Least Privilege (PoLP) are essential. Disabling direct root login via SSH and using
sudofor privilege escalation further secures access. - Automated Security Updates: Configuring tools like
unattended-upgradesensures prompt application of security patches, reducing manual overhead and maintaining a strong security posture.
# Example: Hardening OpenSSH on Ubuntu
# Backup the existing SSH configuration
sudo cp /etc/ssh/sshd_config /etc/ssh/sshd_config.bak
# Edit the SSH configuration file to apply hardening options
sudo nano /etc/ssh/sshd_config
# Recommended hardening options:
# PermitRootLogin no # Disable direct root login
# AllowUsers yourusername # Only allow specific users
# PasswordAuthentication no # Disable password authentication (use SSH keys)
# UsePAM no # Disable Pluggable Authentication Modules
# X11Forwarding no # Disable X11 forwarding
# AllowTcpForwarding no # Disable TCP forwarding
# PermitEmptyPasswords no # Disallow empty passwords
# After making changes, restart the SSH service to apply them
sudo systemctl restart sshd
Network and Access Controls: The Perimeter Defense
Beyond the OS, network and access controls form the perimeter defense:
- DigitalOcean Cloud Firewalls: These project-level firewalls act as security groups, allowing you to centrally manage and enforce rules for inbound and outbound traffic across your Droplets, permitting only necessary communication.
- Virtual Private Cloud (VPC) Integration: Utilizing DigitalOcean's VPC allows for private networking between Droplets, preventing sensitive management interfaces from being exposed to the public internet.
- Multi-Factor Authentication (MFA): Implementing MFA for all access to the DigitalOcean control panel and sensitive systems adds a crucial layer of security against credential compromise.
Application and Service Hardening: Protecting the Workload
Applications and services running on your Droplets also require specific hardening:
- Database and Web Server Security: Apply specific security configurations for databases (e.g., MySQL, PostgreSQL) and web servers (e.g., Apache, Nginx). This includes disabling unused modules, enforcing encryption, and restricting remote access.
- Disable Verbose Error Messages: Prevent information leakage that attackers could exploit by configuring applications to provide generic error messages instead of detailed ones.
- Regular Vulnerability Scanning: Continuously scan installed applications and frameworks for vulnerabilities and apply necessary patches.
The Ethical Hacker's Imperative: Testing and Validation
Simulating Attacks to Strengthen Defenses
From an ethical hacker's perspective, provisioning and hardening are not static tasks but part of an ongoing security lifecycle. The core of this approach is to think like an attacker to identify and remediate vulnerabilities before malicious actors can exploit them. This involves continuous testing and validation of security controls.
Phases of Ethical Hacking in Relation to Provisioning and Hardening
Ethical hackers employ several techniques to assess the security of provisioned and hardened DigitalOcean Droplets:
This mindmap illustrates the interconnected phases of secure server management, emphasizing the role of ethical hacking in validating security measures from provisioning through continuous hardening.
- Reconnaissance: An ethical hacker will first conduct extensive reconnaissance, probing for open ports, identifying default accounts, weak SSH configurations, and outdated OS or applications. Tools like Nmap are frequently used to map the network landscape and identify potential entry points.
- Vulnerability Scanning & Exploitation: Automated vulnerability scanners are employed to identify known misconfigurations, unpatched software, and common vulnerabilities. Following this, an ethical hacker attempts to exploit these identified weaknesses, similar to how a malicious attacker would. This includes testing for weak or reused SSH keys, and instances where password authentication might have been inadvertently re-enabled.
- Privilege Escalation and Persistence: After initial access, the focus shifts to privilege escalation. Ethical hackers test for misconfigurations in sudoers files or weak file permissions that could allow a low-privileged user to gain root access. They also investigate methods for persistence and evasion, looking for backdoors or unmonitored network paths.
- Cloud-Specific Misconfigurations: For DigitalOcean, specific attention is paid to misconfigurations in cloud firewalls, metadata services, and exposed management interfaces, which can lead to lateral movement or privilege escalation within the cloud environment.
Comparative Security Analysis: Provisioning vs. Hardening Focus Areas
A Snapshot of Security Strengths
The radar chart below visually compares the perceived security strengths of various aspects during server provisioning versus server hardening. This analysis is based on typical industry best practices and common attack vectors. Higher values indicate greater security emphasis or effectiveness in that area.
This radar chart provides an analytical comparison of security effectiveness across different domains during the provisioning and hardening phases. It highlights how certain areas are more heavily fortified at specific stages.
Key Areas and Their Security Implications
A Consolidated View of Critical Security Aspects
To further illustrate the comprehensive nature of server provisioning and hardening, the following table summarizes key security aspects, their relevance during each phase, and the implications from an ethical hacker's and cybersecurity professional's viewpoint.
| Security Aspect | Relevance in Provisioning | Relevance in Hardening | Ethical Hacker's Perspective | Cybersecurity Professional's Perspective |
|---|---|---|---|---|
| SSH Key Authentication | Mandatory for initial secure access; disables password login. | Ensures continued secure remote access; periodic key rotation. | Tests for password fallback, weak key strength, key compromise. | Enforces strict key management policies, ensures compliance. |
| Firewall Configuration | Initial port restrictions; DigitalOcean Cloud Firewall setup. | Refining rules, implementing granular controls (e.g., egress filtering). | Probes for open ports, misconfigured rules, bypass opportunities. | Deploys layered firewalls, monitors traffic, ensures network segmentation. |
| Operating System Updates | Selecting current, patched OS images; initial Cloud-Init updates. | Continuous patching and vulnerability management. | Scans for unpatched CVEs, exploits known vulnerabilities. | Automates patch management, tracks patch compliance, applies security baselines. |
| Unnecessary Services/Software | Avoids installing by default; minimal OS image selection. | Disables/removes post-provisioning; continuous auditing. | Enumerates services, looks for exploitable default configurations. | Maintains strict inventory, enforces least functionality principle. |
| User Account Management | Disabling root login; creating least privilege user accounts. | Enforcing strong passwords, MFA, role-based access control. | Tests for default credentials, weak passwords, privilege escalation paths. | Implements IAM solutions, audits user activity, conducts regular access reviews. |
| Logging and Monitoring | Enabling basic logging (e.g., syslog). | Configuring comprehensive audit trails (auditd), SIEM integration, alerts. | Attempts to disable logs, bypass detection, and hide tracks. | Establishes robust logging infrastructure, implements anomaly detection, ensures rapid incident response. |
| Backup and Recovery | Planning for data redundancy during setup. | Regular automated backups, testing recovery procedures. | Assesses data exfiltration opportunities if backups are unsecured. | Ensures immutable backups, tests RTO/RPO, verifies data integrity. |
Deep Dive into Cloud Security Shared Responsibility Model
Understanding Your Role in DigitalOcean Security
When operating in the cloud, particularly with Infrastructure-as-a-Service (IaaS) providers like DigitalOcean, it's crucial to understand the shared responsibility model. DigitalOcean is responsible for the security of the cloud (e.g., the underlying infrastructure, physical security of data centers, network, and virtualization layers). However, you, as the user, are responsible for security in the cloud. This includes the security of your Droplets (OS, applications, data), network configurations, and access management. This distinction is vital for effective server provisioning and hardening.
This video clarifies the shared responsibilities between cloud providers and users, a critical concept for effective cloud security.
From an ethical hacker's viewpoint, the shared responsibility model identifies clear boundaries for testing. While the underlying DigitalOcean infrastructure is generally secure, the ethical hacker focuses on misconfigurations and vulnerabilities within the user's domain—the Droplets themselves, the deployed applications, and the network rules configured by the user. A cybersecurity professional's role is to ensure that all aspects within their responsibility are meticulously secured and regularly audited.
Frequently Asked Questions (FAQ)
Conclusion
Server provisioning and hardening on DigitalOcean, when viewed through the combined lenses of an ethical hacker and a cybersecurity professional, demand a meticulous, proactive, and continuous approach. It's not just about deploying a server but about building a resilient, secure foundation that can withstand sophisticated cyber threats. By integrating security into every step of the provisioning process, adopting comprehensive hardening practices, and continuously validating these defenses through an attacker's mindset, organizations can significantly bolster their cloud security posture on DigitalOcean. This layered and iterative approach is fundamental to safeguarding sensitive data and maintaining operational integrity in the dynamic threat landscape of today.
Recommended Further Exploration
- Advanced Cloud-Init scripts for DigitalOcean security automation
- Implementing Zero-Trust architecture on DigitalOcean Droplets
- Automated vulnerability scanning and penetration testing tools for cloud environments
- Compliance frameworks and their impact on cloud server hardening