
Unlocking IoT Security: How GSMA IoT SAFE Leverages Your SIM Card
Discover the power of IoT SAFE and the crucial role of secure protocols like SCP03, SCP80, and SCP81 in protecting connected devices.
Highlights
- SIM as a Fortress: GSMA IoT SAFE transforms the standard SIM/eSIM/iSIM into a hardware-based Root of Trust, providing a secure foundation for IoT device communication.
- End-to-End Protection: The standard enables secure, encrypted communication channels (like DTLS/TLS) directly between IoT devices and cloud platforms, safeguarding data integrity and confidentiality.
- Standardized Security: IoT SAFE offers a common, scalable mechanism using a dedicated applet on the SIM, simplifying robust security implementation across diverse IoT ecosystems.
Demystifying GSMA IoT SAFE
What Exactly is IoT SAFE?
GSMA IoT SAFE (IoT SIM Applet For Secure End-to-End Communication) is a standard developed by the GSMA (the global organisation representing mobile network operators) to tackle the complex security challenges inherent in the Internet of Things (IoT). Instead of relying on potentially vulnerable software or disparate hardware elements within an IoT device, IoT SAFE leverages the highly secure and ubiquitous SIM card (in its various forms: traditional SIM, embedded SIM/eSIM, or integrated SIM/iSIM) as a hardware-based "Root of Trust".
Essentially, it utilizes a specialized software component, known as an applet, residing securely on the SIM. This applet acts as a protected environment (a secure enclave or "crypto-safe") where critical security operations can be performed. It provides a standardized Application Programming Interface (API) that allows the IoT device's main application or middleware to access these security functions without directly handling sensitive cryptographic keys or processes.
Core Objectives and Advantages
The primary goal of IoT SAFE is to establish robust, end-to-end security for data communications between an IoT device and its corresponding cloud service or backend platform. This means ensuring:
- Device Authentication: Verifying the identity of the IoT device connecting to the network or cloud.
- Data Confidentiality: Encrypting data transmitted over the network (e.g., using DTLS or TLS protocols) so it cannot be read if intercepted.
- Data Integrity: Ensuring that data has not been tampered with during transmission.
- Secure Key Management: Providing a secure way to generate, store, and manage the cryptographic keys needed for authentication and encryption.
By standardizing this approach using the SIM, IoT SAFE offers significant advantages:
- Scalability: Provides a common security framework deployable across billions of diverse IoT devices.
- Hardware Security: Leverages the inherent tamper-resistance and secure processing capabilities of the SIM card, which is significantly more secure than software-only solutions.
- Interoperability: Creates a common standard, reducing fragmentation and simplifying security implementation for device manufacturers and service providers.
- Lifecycle Management: Facilitates secure credential provisioning and management throughout the device's operational life.
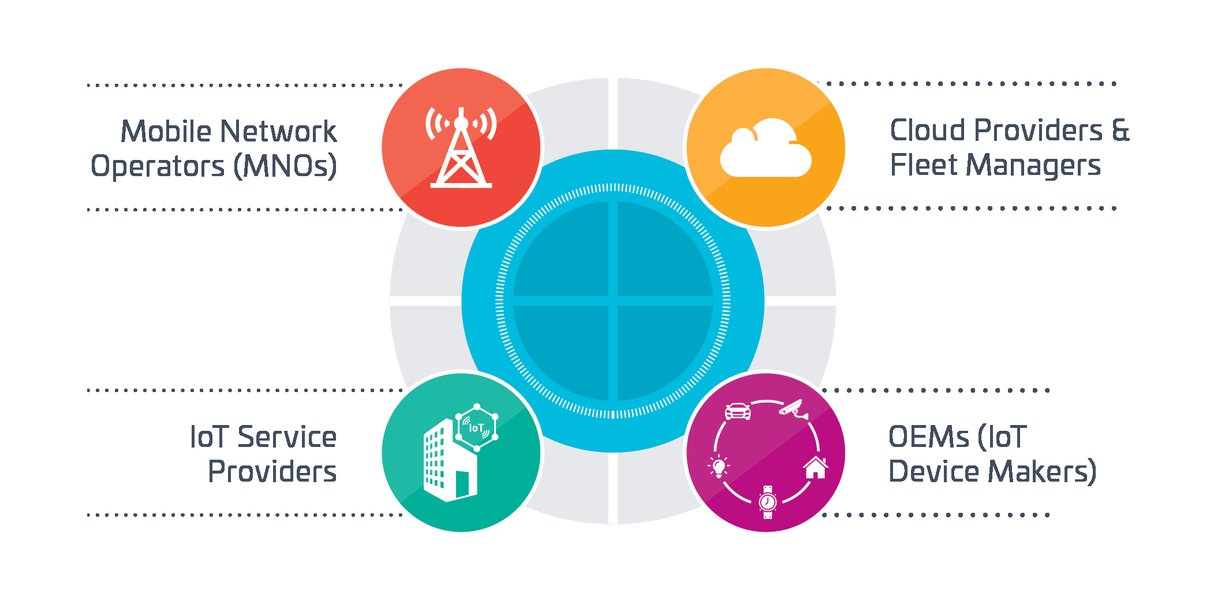
IoT SAFE provides standardized security across diverse IoT application domains.
How it Works: The IoT SAFE Applet
The core component is the IoT SAFE applet installed on the SIM. This applet acts as a dedicated security module. When an IoT device needs to establish a secure connection (e.g., a DTLS session with a cloud server), the device's application communicates with the IoT SAFE applet via the standardized API. The applet then performs the necessary cryptographic operations (like signing challenges for authentication or generating session keys for encryption) using credentials securely stored within the SIM. This offloads the complex and sensitive cryptographic tasks from the main device processor to the secure environment of the SIM.
IoT SAFE supports different security mechanisms, often categorized into types:
- Type I: Primarily uses asymmetric cryptography (e.g., X.509 certificates) for robust authentication, but can also support Pre-Shared Keys (PSK).
- Type II: Relies solely on symmetric Pre-Shared Keys (PSK), often suitable for more resource-constrained IoT devices.
The Role of Secure Channel Protocols (SCPs) in the SIM Ecosystem
Understanding SCPs
Before diving deeper into the IoT SAFE context, it's important to understand Secure Channel Protocols (SCPs) in the world of smart cards, including SIMs. SCPs are standardized methods defined (often by bodies like GlobalPlatform) to establish a secure communication channel between an external entity (like a device's application, a management server, or an OTA platform) and the card itself (the SIM). The primary purpose of an SCP is to protect the commands sent *to* the card and the responses received *from* it, ensuring:
- Confidentiality: Preventing eavesdropping on the data exchanged.
- Integrity: Detecting any modification or tampering of the data.
- Authentication: Verifying that the communication parties are legitimate.
These protocols are fundamental for securely managing applets and data on the SIM, especially when performed remotely (Over-The-Air). Different SCP versions offer varying levels and types of security.
Visualizing the Relationships
The following mindmap illustrates the relationships between IoT security concepts, GSMA IoT SAFE, the SIM, the applet, and the relevant Secure Channel Protocols.
(Requires Secure Channel)"] id1c["Enables End-to-End Security"] id1c1["(D)TLS Sessions"] id1c2["Device Authentication"] id1c3["Data Encryption"] id2["SIM Secure Channel Protocols (SCPs)"] id2a["Purpose: Secure Card Communication"] id2a1["Confidentiality"] id2a2["Integrity"] id2a3["Authentication"] id2b["SCP03"] id2b1["Data Security Focus"] id2b2["Encrypt-then-MAC"] id2b3["Secures Applet Commands/Responses"] id2c["SCP80 / SCP81"] id2c1["Transport Security Focus"] id2c2["Secures Communication Link"] id2c3["Used for OTA / Remote Management
(e.g., SM-SR/SM-DP+)"] id3["Interplay"] id3a["SCPs secure interaction *with* the SIM/Applet"] id3b["IoT SAFE Applet *uses* SIM capabilities
to secure *device-to-cloud* data"] id3c["Layered Security Approach"]
This map highlights that while IoT SAFE focuses on securing the end-to-end IoT data path using mechanisms like TLS/DTLS facilitated by the applet, the SCPs play a crucial role in securely managing the SIM and the applet itself, or protecting the transport layer during certain operations.
Connecting SCPs to the IoT SAFE Applet
Now, let's examine how SCP03, SCP80, and SCP81 specifically relate to the SIM card when it hosts an IoT SAFE applet.
SCP03: Securing Data Interactions with the Applet
SCP03 is a widely adopted Secure Channel Protocol focused on **data security**. It typically uses symmetric keys and an "Encrypt-then-MAC" approach to provide strong confidentiality and integrity protection for the Application Protocol Data Units (APDUs) – the commands and responses exchanged with an applet on the SIM.
Relevance to IoT SAFE:
- Secure Applet Management: While the IoT SAFE applet facilitates secure end-to-end (D)TLS communication for the IoT application, the applet itself might need to be managed, configured, or provisioned with credentials (like keys or certificates). SCP03 provides a standardized, secure way to perform these management operations, ensuring the commands sent to the IoT SAFE applet and the data retrieved from it are protected.
- Protecting Sensitive Operations: When interacting directly with the IoT SAFE applet for tasks like requesting a signature or retrieving a securely stored key handle, SCP03 can secure this communication path between the device's middleware and the applet.
- GlobalPlatform Standard: As a core part of the GlobalPlatform card specifications, SCP03 is a common feature on modern SIMs/eUICC platforms capable of hosting secure applets like IoT SAFE.
SCP80 & SCP81: Securing the Transport Layer
SCP80 and SCP81 are primarily focused on **transport security**. They aim to secure the communication channel at a lower level, often used for Over-the-Air (OTA) communication mechanisms.
- SCP80: Traditionally associated with securing commands sent via SMS (Short Message Service).
- SCP81: Designed for securing communication over HTTPS, often used in the context of eSIM remote provisioning and management (interacting with SM-DP+ and SM-SR servers).
Relevance to IoT SAFE:
- Secure Remote Management: In eSIM (eUICC) environments where IoT SAFE might be deployed, SCP81 is crucial for securing the communication channel between the eSIM and the remote management platforms (like the SM-SR). This ensures that commands related to profile management or potentially applet updates are delivered securely over the network.
- Protecting Provisioning: When credentials needed by the IoT SAFE applet are provisioned remotely onto the SIM/eSIM, SCP80 or SCP81 might be used to secure the transport of these provisioning commands, depending on the delivery mechanism (e.g., SMS or HTTPS).
- Coexistence: While the IoT SAFE standard itself defines APIs for establishing (D)TLS, the underlying platform might still use SCP80/81 for other SIM management functions that coexist with the IoT SAFE applet.
Layered Security in Practice
It's important to understand the distinction: GSMA IoT SAFE defines a standard for using the SIM to secure the *application data channel* between the IoT device and the cloud, primarily leveraging protocols like (D)TLS. The IoT SAFE applet provides the cryptographic services needed for this.
SCPs (like SCP03, SCP80, SCP81), on the other hand, are protocols designed to secure the communication *directly with the SIM card or applets residing on it*, particularly for management, provisioning, or command/response exchange. Therefore, the correlation is often layered:
- You might use SCP03 to securely send a command to the IoT SAFE applet to initiate a (D)TLS handshake.
- You might use SCP81 to secure the transport channel when remotely updating credentials used by the IoT SAFE applet via an eSIM management platform.
- The IoT SAFE applet then uses the securely provisioned credentials to establish the end-to-end secure (D)TLS channel for the actual IoT application data.
While some sources note that IoT SAFE specifications focus primarily on the high-level API for (D)TLS and might not explicitly *mandate* the use of specific SCPs for its core function, these SCPs are established, underlying technologies within the secure SIM ecosystem that are often essential for the secure management and operation of applets like IoT SAFE.
Comparing Secure Channel Protocols
The radar chart below provides a visual comparison of SCP03 and SCP80/81 based on several key characteristics relevant to the SIM and IoT security context. The values represent a relative assessment rather than precise metrics.
This chart illustrates that SCP03 is more focused on securing the actual data exchanged with an applet (higher application layer relevance), making it pertinent for direct interactions with the IoT SAFE applet's functions. SCP80/81 are more about securing the underlying transport path, crucial for remote management and provisioning tasks within the broader SIM ecosystem.
Practical Application & Benefits
Feature Summary Table
The following table summarizes the key features and roles of IoT SAFE and the discussed SCPs in the context of secure IoT communication.
| Feature | GSMA IoT SAFE | SCP03 | SCP80 / SCP81 |
|---|---|---|---|
| Primary Goal | Secure End-to-End IoT data communication (Device-to-Cloud) | Secure communication channel for commands/responses with SIM applets | Secure transport layer for remote SIM communication/management |
| Security Layer Focus | Application Layer (via DTLS/TLS) | Application/Session Layer (Secures APDUs) | Transport Layer (Secures delivery channel, e.g., SMS or HTTPS) |
| Key Mechanism | Uses SIM applet for cryptographic operations (keys, certs, PSK) to establish (D)TLS | Symmetric key cryptography (Encrypt-then-MAC) | Transport-level encryption and integrity protection |
| Main Use Case (IoT Context) | Authenticating device & encrypting application data between device and cloud | Securely managing/interacting with the IoT SAFE applet (or other applets) on the SIM | Secure Over-The-Air (OTA) provisioning or management of SIM/eSIM (e.g., credential updates, profile download) |
| Relevant Standard Body | GSMA | GlobalPlatform | ETSI / 3GPP (historically); SCP81 relevant to GSMA eSIM specs |
Visualizing IoT SAFE Implementation
Understanding how these components fit together is key to appreciating the value of IoT SAFE. The following video from Thales, a key player in digital identity and security, provides a concise overview of the GSMA IoT SAFE standard and its benefits in addressing cybersecurity challenges within the IoT landscape.
This video highlights how IoT SAFE leverages the SIM as a secure foundation, simplifying the process for device manufacturers and service providers to implement strong, scalable security measures. It visually reinforces the concept of using the SIM not just for network connectivity, but as a crucial security anchor for the entire IoT ecosystem, enabling trusted communication from the device right through to the cloud application.

IoT SAFE positions the SIM as a digital safe for securing IoT communications.
Frequently Asked Questions (FAQ)
What is the main benefit of using the SIM as a Root of Trust?
Is IoT SAFE mandatory for all IoT devices?
Can IoT SAFE work without SCPs?
What's the difference between IoT SAFE Type I and Type II applets?
How does IoT SAFE compare to other IoT security solutions?
Recommended Further Exploration
- What are the differences between SIM, eSIM, and iSIM security features?
- How does GSMA IoT SAFE integrate with cloud platforms like AWS IoT or Azure IoT Hub?
- Explore real-world use cases and deployments of GSMA IoT SAFE.
- Compare GlobalPlatform Secure Channel Protocols: SCP02 vs SCP03 vs SCP11.
References
Last updated May 4, 2025