
Unlocking Secure Networks: Real-Life Insights into IPsec
A deep dive into applications, typical use cases, and SA management in IPsec
Key Highlights
- Securing VPNs and Data Transmission: IPsec is extensively utilized for securing site-to-site and remote access VPNs, safeguarding sensitive transactions.
- Dynamic vs Static SAs: Security Associations (SAs) can be dynamically created via IKE or statically configured, with a typical bidirectional pairing for communication.
- Comprehensive SA Management: SAs have predetermined lifetimes and correspond to secure channels at the application layer supported by concrete configuration data and credentials.
Overview of IPsec and Its Real-Life Applications
IPsec (Internet Protocol Security) is a robust suite of protocols designed to enforce secure communications over IP networks by providing confidentiality, integrity, and authentication. It operates primarily at the network layer, securing each IP packet transmitted between hosts. This security mechanism is critical in today’s digital landscape where safeguarding data against interception and tampering is paramount. Various industries, including finance, healthcare, government, and enterprise networks, harness IPsec’s capabilities to bolster their security posture.
Real-Life Use Cases
Securing Virtual Private Networks (VPNs)
One of the most prevalent implementations of IPsec is in VPN configurations. Organizations employ IPsec to create both site-to-site VPNs, connecting multiple geographical branches, and remote access VPNs, where employees securely access central corporate resources from remote or mobile locations. By establishing a secure tunnel, IPsec ensures that data transmitted over untrusted public networks remains encrypted and protected from unauthorized access.
Data Protection for Sensitive Transactions
In industries such as banking, finance, and healthcare, IPsec plays a vital role in safeguarding the transmission of sensitive data. Online banking transactions, for instance, rely on IPsec to secure communications between customer devices and bank servers. Similarly, telemedicine and electronic health records use IPsec to comply with regulatory requirements (like HIPAA) by encrypting patient data during inter-facility transfers.
Government and Military Communications
Security for government and military communications is another critical application. Such entities require stringent data confidentiality and integrity measures, and IPsec’s suite of protocols offers the necessary layer of protection for classified communications, ensuring that sensitive information remains secure even when transmitted over potentially compromised networks.
Internet of Things (IoT) and Enterprise Integration
As enterprises expand their network ecosystems to include IoT devices, IPsec further extends its importance. Not only does it secure data exchanged between traditional computing hosts, but it is also central to protecting communications among embedded devices in a heterogeneous network environment.
Management of IPsec Security Associations (SAs)
Central to IPsec functionality is the concept of Security Associations (SAs), which are agreements between two communicating parties that define the security parameters for their session. These parameters include encryption algorithms, authentication methods, keys, and lifetimes. Effective management of SAs is fundamental in establishing and maintaining secure data communication channels.
Key Aspects of SA Management
1. Number of SA Pairs
In typical IPsec implementations, a pair of hosts maintains two unidirectional SAs: one for outbound traffic and one for inbound traffic. This bidirectional setup means that while transmitting data from Host A to Host B, one SA protects the outgoing packets, and the corresponding SA on the receiving end protects the incoming packets. This approach ensures that security is maintained separately for each direction of traffic, accommodating differing cryptographic requirements if necessary.
2. Creation Method: Dynamic vs. Static
SAs may be established in one of two ways:
- Dynamically Created SAs: Most commonly, SAs are dynamically established using the Internet Key Exchange (IKE) protocol. This automated process facilitates the negotiation of security parameters, encryption keys, and authentication methods.
- Statically Configured SAs: In some scenarios, particularly in networks with predictable traffic patterns or specific security requirements, SAs can be pre-configured. This approach eliminates dynamic negotiation overhead but is generally less flexible.
In practice, IPsec implementations often use a combination of both methods, employing dynamic creation for flexibility and scalability while resorting to static configuration in scenarios that require pre-established security parameters.
3. Application Layer Correspondence
In common use cases, a pair of SAs typically corresponds to a secure communication channel at the application layer. This channel acts as a tunnel through which data flows securely between applications on two hosts. Whether it’s a VPN tunnel facilitating encrypted data transfer or a secure session for a VoIP call, the pair of SAs encapsulates the application layer communications, relaying the underlying transport protocols (like TCP or UDP) securely.
4. Duration and Lifetime of SAs
The lifetime of an SA is determined by specific configuration parameters. Generally, SAs have a defined lifespan measured either in seconds or in the volume of data transmitted, after which the SA expires and must be renegotiated. For many enterprise and VPN configurations, lifespans typically range from several hours to one or more days. This predefined expiration is crucial in ensuring that keys remain fresh and to reduce the risks associated with long-term key exposure.
5. Process for Dynamically-Created SAs
Dynamically-created SAs are established using the Internet Key Exchange (IKE) protocol, which operates in multiple phases:
- Phase 1 (IKE SA Establishment): The hosts authenticate each other and establish a secure, initial channel, known as the IKE SA. This phase lays down the groundwork for further negotiations and ensures that both parties are trusted.
- Phase 2 (IPsec SA Negotiation): Following the secure IKE SA establishment, Phase 2 negotiates the actual security association for IPsec. This involves agreeing on encryption algorithms, authentication methods, and generating shared secret keys. Quick Mode is often referenced during this phase as it handles the negotiation of the IPsec SAs for protecting the actual data traffic.
6. Required Configuration Data and Credentials
For IPsec to function correctly and secure data traffic, the hosts need to be equipped with the necessary configuration data and credentials. These typically include:
- Authentication Methods: This could be either pre-shared keys (PSK) or digital certificates from a Public Key Infrastructure (PKI). The chosen method depends on the security requirements and scalability of the network.
- Encryption and Hashing Algorithms: Both hosts must agree on an encryption standard (such as AES) and a hashing algorithm (such as SHA) to synchronize the secure communication process.
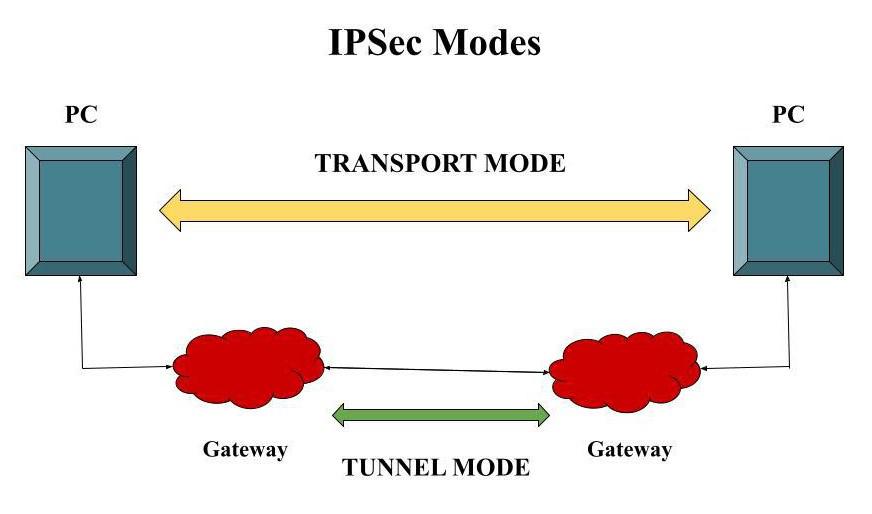
- IPsec Policies and Parameters: These policies dictate which network traffic is to be encrypted and define the parameters for the encryption, including key lifetimes, modes (tunnel or transport), and specifics of the algorithms to be used.
- Network Details: Host IP addresses, port numbers, and identifiers (like Security Parameter Indexes) are essential for matching the proper SA with corresponding traffic.
Comprehensive Comparison Table
| Aspect | Description |
|---|---|
| Number of SA Pairs | Typically two (unidirectional SAs for inbound and outbound traffic) |
| Creation Method | Dynamically created via IKE in most cases; static configuration is also possible |
| Application Layer Correspondence | Represents a secure channel (e.g., VPN tunnel, secure session for VoIP or web applications) |
| Lifetime of SAs | Ranges from several hours to days (based on time or data volume) |
| Dynamic SA Creation Process |
|
| Configuration Data & Credentials |
|
References
- Understanding IPsec: A Deep Dive into Its Architecture and Use Cases - NetSecCloud
- IPsec VPNs: Ensuring Secure Communication - Uplevel Systems
- What is IPsec? | How IPsec VPNs work - Cloudflare
- IPsec Security Associations Overview - Juniper Networks
- Security associations (SA) in IPsec VPNs - StoneSoft
Recommended Related Queries
Last updated March 25, 2025