
Understanding the Use of /dev/mem in Linux Drivers
A Comprehensive Guide to Direct Memory Access and Hardware Interaction
Key Takeaways
- Direct Memory Access: /dev/mem provides Linux drivers with the capability to access physical memory directly, essential for memory-mapped I/O operations.
- Driver Development and Debugging: It serves as a valuable tool for developers to prototype, debug, and interact with hardware without the need for kernel modules.
- Security and Stability Risks: While powerful, the use of /dev/mem introduces significant security vulnerabilities and potential system instability if not managed correctly.
Introduction to /dev/mem
/dev/mem is a special character device file in Linux that provides user-space applications with direct access to the system's physical memory. This access bypasses the traditional virtual memory management provided by the kernel, allowing applications and drivers to interact directly with hardware components mapped into the system's memory space.
Reasons Linux Drivers Use /dev/mem
1. Direct Access to Physical Memory
One of the primary reasons Linux drivers utilize /dev/mem is to gain direct access to the system's physical memory. This is particularly crucial for interacting with memory-mapped I/O (MMIO) regions, where hardware devices map their control registers into the system's memory space. By accessing these regions directly, drivers can read from or write to hardware registers, enabling precise control over the hardware.
2. Interaction with Hardware
/dev/mem facilitates direct communication with hardware components, such as network cards, graphics processors, and other peripheral devices. This is especially useful in scenarios where the standard kernel APIs do not provide the necessary functionality or when working with custom or proprietary hardware that requires bespoke interaction methods.
3. Driver Development and Debugging
During the development phase, /dev/mem serves as an invaluable tool for debugging and testing. Developers can inspect and modify physical memory regions to diagnose issues, test hardware interactions, and prototype driver functionalities without the overhead of writing and loading kernel modules. This expedites the development process by allowing rapid iterations and real-time observations of hardware behavior.
4. Legacy and Specialized Use Cases
In legacy systems or specialized applications, such as embedded systems, /dev/mem provides the necessary access mechanisms for tasks like BIOS emulation, DOS compatibility, or direct hardware register manipulation. These use cases often require low-level memory access that is not feasible through higher-level abstractions.
How /dev/mem is Utilized
Memory Mapping with mmap()
Linux drivers typically use the mmap() system call in conjunction with /dev/mem to map physical memory regions into the driver's virtual address space. This mapping allows drivers to interact with hardware registers as if they were standard memory locations within their process. The following C code snippet demonstrates how a driver might map a physical address:
#include <fcntl.h>
#include <sys/mman.h>
#include <stdio.h>
#include <stdlib.h>
#define MAP_SIZE 4096UL
#define PHYSICAL_ADDRESS 0x1C000000
int main() {
int fd = open("/dev/mem", O_RDWR | O_SYNC);
if (fd == -1) {
perror("open");
exit(EXIT_FAILURE);
}
void *map_base = mmap(0, MAP_SIZE, PROT_READ | PROT_WRITE, MAP_SHARED, fd, PHYSICAL_ADDRESS);
if (map_base == MAP_FAILED) {
perror("mmap");
close(fd);
exit(EXIT_FAILURE);
}
// Interact with the mapped memory
volatile unsigned int *reg = (volatile unsigned int *)map_base;
unsigned int value = reg[0]; // Read a register
reg[0] = 0xFF; // Write to a register
// Cleanup
if (munmap(map_base, MAP_SIZE) == -1) {
perror("munmap");
}
close(fd);
return 0;
}Low-Level Memory Access
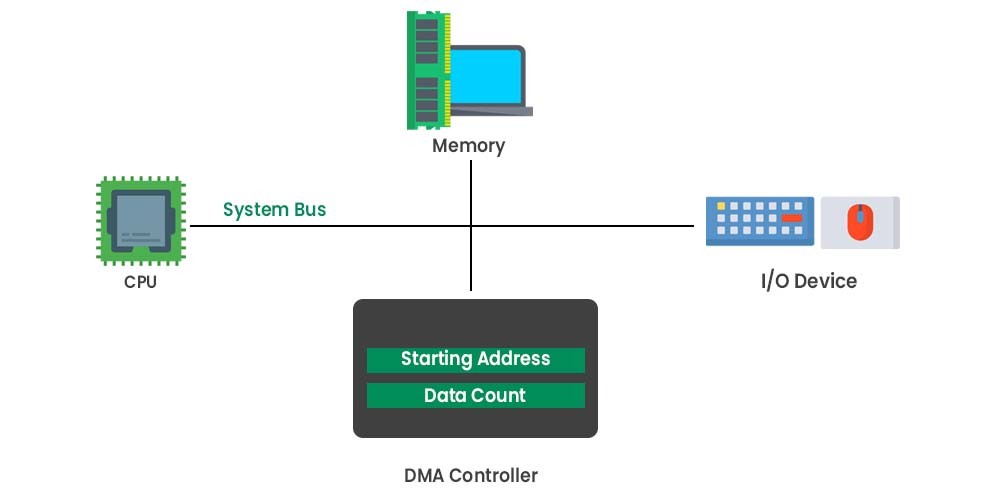
By accessing physical memory directly, drivers can perform operations such as configuring device registers, initiating DMA (Direct Memory Access) transfers, and handling interrupts. This level of control is essential for optimizing performance and ensuring that the hardware operates as intended.
Implementation as a Character Device
/dev/mem is implemented as a character device within the Linux kernel. Unlike block devices, which are used for storage media and require buffering, character devices provide unbuffered, direct access to hardware. This makes them suitable for applications that need real-time interaction with hardware components.
Root Privileges Requirement
Accessing /dev/mem typically requires root privileges. This restriction is in place to prevent unauthorized or malicious access to critical system memory, which could compromise system integrity and security.
Risks and Limitations of Using /dev/mem
Security Risks
Providing direct access to physical memory poses significant security vulnerabilities. Unauthorized access can lead to the exposure or manipulation of sensitive data, including kernel space memory, which can be exploited to compromise the entire system. Malicious actors gaining access to /dev/mem can manipulate hardware registers to perform attacks such as privilege escalation or data theft.
Kernel Protections and Configurations
Modern Linux kernels incorporate several protections to mitigate the risks associated with /dev/mem. The CONFIG_STRICT_DEVMEM configuration option restricts access to non-sensitive memory regions, limiting the functionality available through /dev/mem. Disabling these protections can restore full access but at the expense of increased security risks. Administrators must carefully balance the need for access with the potential threats posed by its misuse.
System Stability and Integrity
Direct manipulation of physical memory can lead to system instability. Incorrect reads or writes to critical memory regions can corrupt system state, cause crashes, or lead to undefined behavior. Such actions bypass the kernel's safety mechanisms, making it easier to inadvertently introduce bugs or vulnerabilities.
Not a Substitute for Proper Kernel Drivers
While /dev/mem offers powerful access capabilities, it does not provide the structured and secure environment that proper kernel drivers offer. Kernel drivers handle concurrency, manage resources, and integrate seamlessly with the operating system's subsystems, ensuring stability and security. Relying solely on /dev/mem can lead to fragmented and less maintainable codebases.
Best Practices for Using /dev/mem
When to Use /dev/mem
Use /dev/mem sparingly and only when necessary. It is most appropriate for:
- Prototyping and rapid development phases where quick access to hardware is required.
- Debugging hardware interactions without the overhead of kernel module development.
- Legacy support for applications that depend on direct memory access.
- Embedded systems with specific hardware interaction requirements.
Prefer Proper Kernel Drivers for Production
For long-term and production environments, developing proper kernel drivers is the recommended approach. Kernel drivers offer:
-
Enhanced security through controlled access mechanisms.
-
Improved stability by integrating with the kernel's resource management systems.
-
Better performance through optimized interactions with hardware.
-
Maintainability and scalability, facilitating easier updates and feature additions.
Implement Access Controls
Ensure that access to /dev/mem is tightly controlled. Only trusted and necessary processes should have the required privileges to interact with this device. Implementing strict access controls minimizes the risk of unauthorized access and potential exploitation.
Utilize Kernel Configuration Options
Leverage kernel configuration options such as CONFIG_STRICT_DEVMEM to limit the scope of accessible memory regions. This reduces the attack surface and mitigates potential security vulnerabilities associated with unrestricted memory access.
Technical Considerations
Page Alignment and Memory Access
When mapping physical memory regions using /dev/mem, it is essential to ensure that the physical addresses are page-aligned. Misaligned accesses can lead to unexpected behavior or errors. Additionally, drivers must be cautious when performing read and write operations to avoid crossing page boundaries inadvertently.
Cache Coherence
Directly accessing memory via /dev/mem can bypass the CPU's cache, leading to cache coherence issues. Developers must manage cache consistency manually to prevent data corruption or inconsistent state between the cached data and the actual memory contents. Utilizing appropriate flags, such as O_SYNC, when opening /dev/mem can help mitigate some of these issues by ensuring that memory operations are performed synchronously.
Error Handling and Recovery
Robust error handling mechanisms should be implemented when interacting with /dev/mem. This includes verifying successful memory mappings, handling exceptions gracefully, and ensuring that resources are appropriately released to maintain system stability.
Performance Implications
While /dev/mem allows for low-latency access to hardware, it can introduce performance overhead if not used judiciously. Frequent context switches between user-space and kernel-space or excessive memory mapping operations can degrade system performance. Optimizing access patterns and minimizing unnecessary operations can help maintain optimal performance levels.
Conclusion
/dev/mem is a powerful tool in the Linux ecosystem, providing drivers and developers with direct access to the system's physical memory. This capability is essential for tasks that require precise hardware interaction, debugging, and rapid prototyping. However, the use of /dev/mem comes with significant risks, including security vulnerabilities and potential system instability. As such, it should be employed judiciously and primarily within controlled environments. For production systems and long-term solutions, developing proper kernel drivers remains the best practice, ensuring security, stability, and maintainability.
References
Last updated January 24, 2025