
Creating a Parserless Network Log and Security Alert Ingestion Platform
Build a scalable, flexible, and efficient security monitoring system without predefined parsers.
Key Takeaways
- Schema-on-Read Approach: Ingest logs in their raw format and parse them during query time, enhancing flexibility and reducing maintenance.
- Unified Data Model: Standardize log formats using models like JSON or CEF to ensure consistency across diverse log sources.
- Scalable and Secure Architecture: Utilize distributed systems and robust security measures to handle high log volumes and protect sensitive data.
1. Define Scope and Requirements
Identify Objectives and Log Sources
Begin by determining the specific goals of your ingestion platform. Whether it's for real-time threat detection, compliance monitoring, or forensic analysis, clearly defining your objectives will shape the architecture and components of your system.
- Log Sources: Catalog the types of logs you intend to ingest, such as firewall logs, IDS/IPS alerts, endpoint protection logs, and other network device logs.
- Data Volume: Estimate the expected volume of logs to ensure the platform can scale accordingly.
- Use Cases: Outline the primary use cases, including threat detection, incident response, compliance auditing, and operational monitoring.
2. Architectural Design
Plan the Framework for Ingestion and Processing
A well-thought-out architectural design is crucial for a parserless ingestion platform. Focus on flexibility, scalability, and efficiency to handle diverse log formats and high data throughput.
- Distributed Collector System: Implement collectors positioned close to log sources to minimize latency and ensure efficient log transmission.
- Event Streaming: Utilize technologies like Apache Kafka or Azure Event Hubs to manage high-throughput data ingestion and buffering.
- Multiple Input Protocols: Ensure the system supports various input protocols such as Syslog, HTTP/S, TCP, and UDP to accommodate different log sources.
3. Data Ingestion Framework
Adopt a Schema-on-Read and Unified Data Model
Choosing the right data ingestion framework is essential for handling raw logs without predefined parsers. A schema-on-read approach allows logs to be ingested in their native format and parsed as needed during analysis.
- Schema-on-Read: Ingest logs without applying any parsing rules upfront. Parsing is deferred until query time, providing flexibility in handling diverse log formats.
- Unified Data Model: Standardize log formats using models like JSON, CEF (Common Event Format), or ASIM to ensure consistency and ease of querying across different log types.
- Ingestion Tools: Leverage existing tools such as Fluentd, Logstash, Vector, Google Security Operations, Azure Sentinel, or OpenObserve to facilitate log ingestion.
4. Implementing a Parserless Ingestion Pipeline
Ingest, Enrich, and Store Raw Logs
The ingestion pipeline is the backbone of your platform, responsible for collecting, enhancing, and storing logs efficiently.
- Raw Log Ingestion: Collect logs in their raw format using scalable agents like Fluentd or Logstash. Ensure that the agents can handle multiline logs and varying formats without mandatory transformations.
- Metadata Enrichment: Enhance raw logs by adding metadata such as timestamps, source IPs, log types, and other relevant attributes during ingestion. This facilitates efficient querying and analysis later.
- Storage Solutions: Store enriched logs in scalable data lakes or log management platforms like Elasticsearch, Splunk, OpenSearch, or object storage solutions like AWS S3. Opt for schema-less storage to accommodate varied log formats.
5. Dynamic Parsing and Field Extraction
Enable On-Demand Parsing Using Advanced Techniques
Without predefined parsers, it's crucial to have mechanisms that allow for dynamic extraction of relevant fields from raw logs during query time.
- Dynamic Parsing: Implement a query-time parsing engine that can extract necessary fields from raw logs on the fly. Tools like OpenObserve or CrowdStrike Falcon LogScale can facilitate this functionality.
- Field Extraction Techniques: Utilize regular expressions, machine learning models, or natural language processing (NLP) to dynamically extract structured data from unstructured logs.
- Pattern Matching: Apply pattern matching techniques to identify and extract relevant information without the need for static parsing rules.
6. Automating Alert Ingestion
Streamline Security Alert Integration
Automating the ingestion of security alerts ensures that your platform can respond to threats in real-time without manual intervention.
- Alert Forwarding: Configure your Security Information and Event Management (SIEM) or other security tools to forward alerts to the ingestion platform in standardized formats like JSON or CEF.
- Alert Enrichment: Enhance alerts with contextual data such as threat intelligence, asset information, and geolocation data to improve the accuracy and relevance of alert analysis.
7. Building Analytics and Visualization
Create Interactive Dashboards and Detection Mechanisms
Effective analytics and visualization tools are essential for interpreting log data and identifying potential security threats.
- Dashboards: Develop comprehensive dashboards using tools like Grafana, Kibana, or OpenObserve to visualize log data and security alerts. Customizable dashboards enable users to monitor key metrics and trends effortlessly.
- Threat Detection: Implement machine learning algorithms or rule-based systems to identify anomalies and potential threats within the log data. Continuous improvement of detection models enhances the platform's ability to respond to evolving threats.
- Incident Response Integration: Integrate the platform with incident response tools to automate actions based on detected threats, streamlining the response process and minimizing reaction times.
8. Ensuring Scalability and Security
Design for Growth and Protect Sensitive Data
Scalability and security are paramount for maintaining the effectiveness and integrity of your ingestion platform.
- Scalability: Utilize distributed systems and cloud-native services to handle large volumes of log data. Implement horizontal scaling strategies to accommodate increasing data loads without compromising performance.
- Security Measures: Encrypt log data both in transit and at rest to protect sensitive information. Implement robust access controls and role-based access to ensure that only authorized personnel can access or modify log data.
- Data Segregation: If the platform supports multiple teams or organizations, enforce data segregation through multi-tenancy features to maintain data privacy and integrity.
9. Monitoring and Optimization
Maintain Performance and Adapt to Feedback
Continuous monitoring and optimization ensure that the platform remains efficient and responsive to user needs.
- Performance Monitoring: Regularly monitor the performance of the ingestion pipeline, tracking metrics such as latency, throughput, and error rates. Use these insights to identify and address bottlenecks.
- Feedback Loop: Establish a feedback mechanism where analysts and automated systems can provide input on the ingestion and parsing processes. Utilize this feedback to refine and enhance the platform's capabilities.
- Resource Optimization: Optimize resource allocation based on usage patterns and performance metrics to ensure cost-effectiveness and optimal performance.
10. Compliance and Auditing
Adhere to Regulatory Standards and Ensure Data Integrity
Maintaining compliance with regulatory standards is essential for organizations subject to frameworks like GDPR, HIPAA, or ISO 27001.
- Log Retention: Retain logs for the duration required by relevant compliance frameworks. Ensure that storage solutions are configured to maintain logs for the necessary periods.
- Immutable Logs: Implement log immutability to prevent tampering, ensuring that logs remain trustworthy for audits and investigations.
- Audit Trails: Maintain comprehensive audit logs of platform usage, capturing who accessed what data and when. This enhances accountability and traceability.
11. Handling Challenges and Solutions
Address Common Issues in Parserless Ingestion
Creating a parserless platform comes with its unique set of challenges. Proactively addressing these issues ensures the platform's reliability and effectiveness.
11.1 Handling Unstructured Data
- Challenge: Managing logs that lack a consistent structure increases the complexity of processing and querying.
- Solution: Implement dynamic field extraction techniques using user-defined queries, regular expressions, or machine learning models to parse data on demand.
11.2 Scalability
- Challenge: High log volumes can create ingestion bottlenecks and escalate storage costs.
- Solution: Optimize ingestion pipelines with backpressure mechanisms, adopt distributed architectures, and leverage cloud services that support automatic scaling to handle increased loads efficiently.
11.3 Real-Time Alerting
- Challenge: Without predefined parsers, real-time alerting may suffer from latency due to the need for runtime parsing.
- Solution: Integrate lightweight parsers for frequently used log dimensions such as source IPs or ports to expedite real-time alert generation.
12. Core Components and Technologies
Building Blocks of the Ingestion Platform
| Component | Description | Recommended Technologies |
|---|---|---|
| Data Collectors | Agents that collect logs from various sources and forward them to the ingestion pipeline. | Fluentd, Logstash, Vector |
| Event Streaming | Handles high-throughput data ingestion and buffering before processing. | Apache Kafka, Azure Event Hubs |
| Storage Solution | Stores raw and enriched logs in a scalable and efficient manner. | Elasticsearch, OpenSearch, AWS S3, InfluxDB |
| Search Index | Enables rapid querying and retrieval of log data. | Elasticsearch, OpenSearch |
| Alert Correlation Engine | Analyzes logs to identify patterns and correlate alerts for threat detection. | Custom ML Models, Rule-Based Engines |
| API Gateway | Facilitates integration with external tools and provides access to log data. | RESTful APIs, GraphQL |
| Web Interface | Provides a user-friendly interface for visualization and interaction with log data. | Kibana, Grafana, OpenObserve |
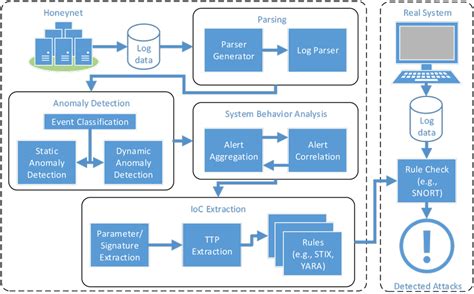
13. Real-Time Processing and Anomaly Detection
Leveraging Stream Processing for Immediate Insights
Real-time processing is vital for timely threat detection and response. Implementing efficient stream processing pipelines enables immediate analysis of incoming log data.
- Stream Processing: Utilize frameworks like Apache Flink or Kafka Streams to process logs in real-time, allowing for instant analysis and alerting.
- Anomaly Detection: Deploy machine learning models to identify deviations from normal behavior patterns, flagging potential security incidents.
- Pattern Matching: Apply pattern recognition techniques to detect suspicious activities such as repeated failed login attempts or unusual network traffic.
14. Security Features
Protecting the Integrity and Confidentiality of Log Data
Ensuring the security of your ingestion platform is paramount to protect sensitive information and maintain trust.
- Encryption: Encrypt log data both at rest using algorithms like AES and in transit using protocols like TLS to safeguard against unauthorized access.
- Role-Based Access Control (RBAC): Implement RBAC to restrict access to log data based on user roles and responsibilities.
- Audit Logging: Maintain detailed audit logs of platform activities, capturing user actions and system events to ensure accountability.
- Source Verification: Authenticate log sources to prevent the ingestion of malicious or tampered logs.
- Data Retention Policies: Define and enforce data retention policies to comply with regulatory requirements and manage storage efficiently.
15. Alert Management
Efficient Handling and Routing of Security Alerts
Effective alert management ensures that security teams can respond promptly and appropriately to potential threats.
- Threshold-Based Alerts: Define thresholds for specific log patterns to trigger alerts when breached, such as a certain number of failed login attempts within a timeframe.
- Statistical Anomaly Detection: Use statistical models to identify outliers and unusual patterns that may indicate security incidents.
- Alert Aggregation and Deduplication: Consolidate similar alerts to reduce noise and prevent alert fatigue among security analysts.
- Notification Channels: Support multiple notification channels like email, Slack, and webhooks to ensure alerts reach the appropriate personnel promptly.
- Severity Levels and Routing: Categorize alerts based on severity and implement routing rules to direct them to the relevant teams or individuals for action.
16. API-Driven and Visual Analytics Dashboard
Facilitating User Interaction and Data Exploration
A robust API and intuitive dashboard empower users to interact with log data seamlessly and derive meaningful insights.
-
Query Interface: Provide a flexible query interface that allows users to craft custom searches and filters. Tools like Kibana or OpenObserve enable advanced querying capabilities.
-
APIs for Data Access: Develop RESTful APIs or GraphQL endpoints to allow programmatic access to raw and processed log data, facilitating integrations with other tools and systems.
-
Visualizations: Create rich visualizations such as charts, graphs, and heatmaps using dashboarding tools like Grafana or Tableau to represent log data trends and patterns effectively.
17. References
Conclusion
Building a parserless network log and security alert ingestion platform involves careful planning and the integration of various components to ensure flexibility, scalability, and security. By adopting a schema-on-read approach, standardizing data models, and leveraging advanced technologies for dynamic parsing and real-time processing, organizations can create robust platforms that effectively monitor and analyze log data without the overhead of maintaining predefined parsers. Ensuring scalability and security, coupled with comprehensive analytics and visualization tools, empowers security teams to respond swiftly to emerging threats and maintain a strong security posture.
Last updated January 19, 2025