
Building a Secure and Efficient Case Management Platform
A Comprehensive Flow Diagram and Architectural Overview
Key Highlights of the Secure Case Management Platform Architecture
- Robust Security: The architecture prioritizes security through measures like RBAC, encrypted transfers, audit logs, and secure storage for sensitive data.
- Asynchronous Processing: Celery is leveraged for background tasks such as PDF generation and report creation, ensuring the platform remains responsive.
- Structured Data Management: PostgreSQL serves as the central database for structured data, while MinIO handles document and evidence storage.
This document outlines the architecture and process flow for a secure case management platform, incorporating various components to handle user interaction, case creation, evidence management, workflows, inter-agency communication, legal processes, reporting, and comprehensive auditing and security measures. The design emphasizes security, efficiency, and scalability through the strategic use of technologies like React, Django, PostgreSQL, MinIO, Celery, and dedicated security layers.
Detailed Flow Diagram of the Secure Case Management Platform
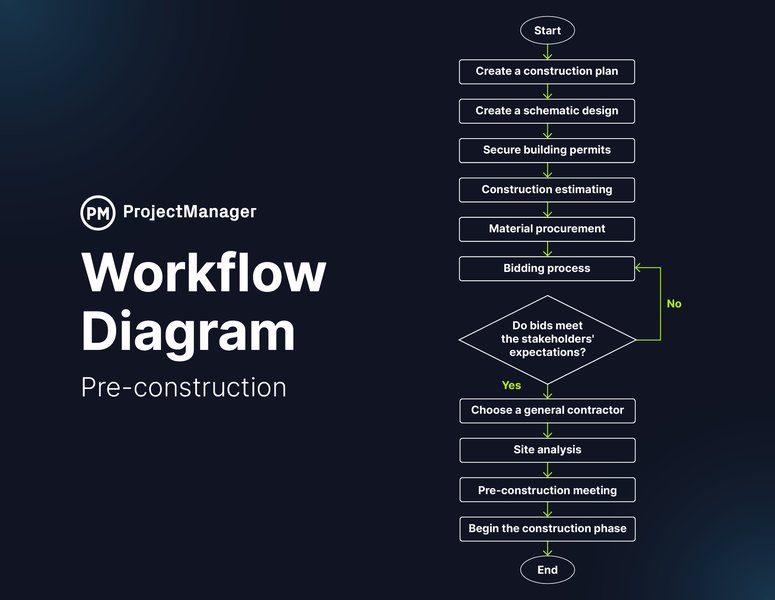
The following diagram illustrates the interconnectedness of the various components and the flow of information within the secure case management platform.
Conceptual Flow of Case Management Processes
Component Breakdown and Interactions
Let's delve deeper into each component and its role within the platform.
1. User Authentication and Access Control
Secure User Login and Role-Based Access
The platform initiates with user authentication via a React user interface. This front-end interacts with a Django backend responsible for handling user logins and implementing Role-Based Access Control (RBAC). Django's built-in authentication and authorization frameworks are leveraged to define roles, assign permissions, and control access to specific parts of the application, ensuring that users only have access to the data and functionalities relevant to their role. All login attempts and authentication-related actions are meticulously recorded in audit logs within the PostgreSQL database for security and compliance purposes. This provides a verifiable trail of user activity.
Illustration of Case Management Principles

2. Case Creation and Initial Data Handling
Streamlined Case Initiation Process
Case creation is facilitated through user-friendly forms within the React UI. Upon submission, the structured case data is sent to the Django backend and stored securely in the PostgreSQL database. Simultaneously, any uploaded documents associated with the case are directed to MinIO, a high-performance, distributed object storage system compatible with Amazon S3. Alerts related to case creation or initial data handling are managed and potentially triggered via Minos, ensuring stakeholders are notified as necessary. This separation of structured data and unstructured documents optimizes storage and retrieval.
3. Evidence Management with Security Layers
Secure Storage and Processing of Evidence
Evidence uploaded to the platform follows a secure workflow. The evidence files are stored in MinIO buckets. Metadata and logs related to the uploaded evidence, including who uploaded it and when, are recorded in PostgreSQL. A critical security layer involves a virus scan on uploaded evidence to prevent malicious content from entering the system. Furthermore, version control is implemented for evidence files stored in MinIO, allowing for tracking changes and reverting to previous versions if necessary. This ensures the integrity and security of sensitive evidence.
Overview of a Secure Case Management Platform
4. Workflow Management and Task Execution
Managing Case Lifecycle and Background Tasks
The case management process is driven by defined workflow states managed within the Django application. These states, such as "Under Review" and "Approved," represent the different stages a case progresses through. Tasks associated with these workflow states, particularly long-running or asynchronous operations, are offloaded to Celery workers. This ensures that the main Django application remains responsive. Examples of Celery tasks in this context could include generating reports or processing data. Signed reports, once finalized, are stored securely in MinIO.
Celery is a powerful distributed task queue that allows for executing tasks asynchronously, either on a schedule or in response to events. Integrating Celery with Django involves configuring Celery to use Django models for storing task results and setting up worker processes to execute the tasks. This is particularly useful for operations that might take a significant amount of time, preventing the web server from being tied up.
# Example Celery task in Django
from celery import shared_task
from .models import Case
@shared_task
def process_case_review(case_id):
try:
case = Case.objects.get(id=case_id)
# Perform review processing
case.status = 'Approved'
case.save()
return f"Case {case_id} approved."
except Case.DoesNotExist:
return f"Case {case_id} not found."
5. Secure Inter-Agency Communication
Facilitating Collaboration with External Parties
Inter-agency communication and document uploads are handled through a dedicated REST API. This API ensures that data transfer between agencies is secure, utilizing encrypted transfer protocols to protect sensitive information during transit. Alerts related to inter-agency interactions or document exchanges are managed via Minos, providing timely notifications to relevant personnel. This component is crucial for collaborative investigations and information sharing while maintaining data security.
6. Legal Process Automation
Automating Legal Document Generation and Distribution
The generation of legal summons, triggered from within the Django application, is automated using Celery. A Celery task is responsible for generating the PDF document of the legal summons. Once generated, the PDF is stored securely in MinIO. Alerts related to the issuance of legal summons or their status are sent via NIC APIs, integrating with external notification systems to ensure legal processes are followed and stakeholders are informed.
7. Dashboards and Reporting
Visualizing Data and Generating Reports
Dashboards provide users with a centralized view of key metrics and case summaries. These dashboards pull data via the Django backend, which queries the PostgreSQL database. Charts are rendered within the UI to visualize trends and provide insights into case volumes, statuses, and other relevant statistics. More detailed reports can be generated via Celery tasks, allowing for the creation of complex documents without impacting the performance of the interactive dashboards. These reports, once generated, can also be stored in MinIO for easy access and archiving.
8. Comprehensive Auditing and Security Measures
Maintaining Security and Accountability
A fundamental aspect of this secure case management platform is comprehensive auditing and security. All actions performed within the platform, from user logins to case modifications and evidence handling, are meticulously logged. Audit logs are primarily stored and managed within the PostgreSQL database, providing a secure and centralized record of all activities. Regular SSL checks are performed to ensure secure communication channels. Furthermore, logs are periodically sent to a secure node for long-term storage and analysis, enhancing the platform's security posture and facilitating forensic investigations if needed.
Key Technology Components
The platform relies on a combination of technologies to deliver its functionality and security features.
| Component | Primary Role | Key Features Utilized |
|---|---|---|
| React | User Interface | Component-based UI development |
| Django | Backend Framework | Authentication, RBAC, ORM, API development, Workflow management |
| PostgreSQL | Database | Structured data storage, Audit logs |
| MinIO | Object Storage | Document and evidence storage, Version control |
| Celery | Asynchronous Task Queue | Background task execution (PDF generation, reporting) |
| Minos | Alerting System | Managing and triggering alerts |
| NIC APIs | External Integration | Sending external notifications (e.g., legal summons alerts) |
Additional Security Considerations
Beyond the core components, several other security considerations are integral to the platform's design:
Data Encryption
Sensitive data, both in transit and at rest, is encrypted. This includes encrypted transfer for inter-agency communication and secure storage mechanisms within PostgreSQL and MinIO.
Access Controls and Permissions
Granular access controls, implemented through Django's RBAC, ensure that users can only access information and perform actions that are explicitly permitted by their role. This minimizes the risk of unauthorized data access or modification.
Regular Security Audits
Periodic security audits and vulnerability assessments are crucial to identify and address potential weaknesses in the platform's architecture and code. The comprehensive audit logs stored in PostgreSQL are invaluable for these assessments.
Secure Deployment and Infrastructure
The security of the underlying infrastructure where the platform is deployed (e.g., servers, network) is paramount. This includes secure configurations, regular patching, and monitoring for suspicious activity. Containerization with Docker and orchestration with Kubernetes, as mentioned in some sources, can contribute to a more secure and manageable deployment.
Frequently Asked Questions
What is Role-Based Access Control (RBAC) in the context of this platform?
RBAC is a method of restricting system access to authorized users based on their role within the organization. In this platform, Django's built-in features are used to define roles (e.g., investigator, manager, legal counsel) and assign specific permissions to each role, ensuring users only have access to the data and functions they need.
Why is Celery used for certain tasks?
Celery is used to handle tasks that are time-consuming or should not block the main application process. This includes generating large reports, creating PDF documents, or performing background data processing. By offloading these tasks to Celery workers, the platform's responsiveness for interactive user sessions is maintained.
How is data secured in transit and at rest?
Data is secured in transit through encrypted transfer protocols, particularly for inter-agency communication. Data at rest is secured through the inherent security features of PostgreSQL and MinIO, including access controls and potentially encryption configured at the storage level.
What role do audit logs play in the platform's security?
Audit logs provide a comprehensive record of all user activities and system events. This is crucial for security monitoring, detecting suspicious behavior, investigating security incidents, and ensuring compliance with regulations. The logs stored in PostgreSQL serve as the primary source for auditing.
How does the platform handle inter-agency communication securely?
Inter-agency communication is handled through a dedicated REST API that utilizes encrypted transfer protocols. This ensures that sensitive data exchanged between agencies remains confidential and protected during transmission.
References
Last updated May 9, 2025