
Unlocking Pandora's Box: The Grave Security Risks of Kernel-Level Access
Why the highest privilege level in your OS is also its greatest potential vulnerability.
Kernel-level access represents the highest privilege tier within an operating system. The kernel acts as the core, managing essential system resources, hardware interactions, and process execution. Granting software access at this level allows it to operate with virtually unrestricted permissions, directly interfacing with the system's fundamental components. While necessary for many legitimate functions, such as device drivers and advanced security software, this profound access level carries significant security implications if misused or compromised.
Highlights: Key Security Implications
- Complete System Compromise: Attackers exploiting kernel vulnerabilities can gain total control, bypassing security measures, manipulating system processes, accessing sensitive data, and installing persistent malware like rootkits.
- System Instability and Failure: Faulty or malicious kernel-level code can lead to critical system errors, performance degradation, denial of service, crashes (like the infamous Blue Screen of Death), and potential data loss.
- Evasion of Security Tools: Malicious actors with kernel access can disable or manipulate security software (antivirus, EDR) that often relies on the same privilege level, rendering them ineffective.
Understanding Kernel-Level Access
The Core of the Operating System
Think of the operating system as having distinct layers of privilege. At the top is the user space, where applications and regular user processes run with limited permissions. Below this lies the kernel space, the domain of the operating system's kernel. The kernel is the central module responsible for:
- Managing memory allocation
- Scheduling CPU time for processes
- Handling input/output (I/O) requests from software
- Interfacing directly with hardware components (CPU, RAM, disk drives, network cards)
- Enforcing security policies
Software operating with kernel-level access can execute commands directly within this privileged space, bypassing many of the restrictions imposed on user-space applications. This is why device drivers, core system services, and certain types of security software (like some antivirus engines and Endpoint Detection and Response - EDR solutions) require kernel access to function correctly.
Why is Kernel Access Powerful and Dangerous?
The power of kernel access stems from its unrestricted control. A program with this level of privilege can:
- Read or modify any part of the system's memory, including data belonging to other processes or the kernel itself.
- Communicate directly with hardware devices.
- Load or unload kernel modules (drivers).
- Modify critical system files and configurations.
- Start, stop, or alter the behavior of any process on the system.
- Intercept network traffic or system calls.
This power makes it an attractive target for attackers. If malicious code can achieve kernel-level execution, it gains the ability to fundamentally compromise the system's integrity, security, and stability.
The Spectrum of Kernel-Level Threats
Exploiting vulnerabilities to gain kernel-level access can lead to a cascade of severe security consequences. Attackers constantly probe for weaknesses in kernel code and kernel-mode drivers.
Unauthorized Access and Privilege Escalation
Gaining the Keys to the Kingdom
Many attacks start with compromising a user-level process. However, the ultimate goal is often to escalate privileges to the kernel level. Vulnerabilities like use-after-free errors (e.g., CVE-2024-1086 in netfilter, CVE-2024-4011) or race conditions (like the "Dirty COW" vulnerability affecting copy-on-write) allow local users or processes to execute code with kernel privileges. Once an attacker achieves this, they effectively own the system.
Arbitrary Code Execution
Running Malicious Commands Unchecked
Certain kernel flaws allow attackers, sometimes even remotely, to execute arbitrary code within the kernel's context. Examples include vulnerabilities in drivers (like `iwch_cm.c`) or network stack components (`__sys_recvnnsg` in `net/socket.c`, or the SMB2 vulnerability CVE-2022-47939 in ksmbd). This is one of the most critical types of vulnerabilities, as it grants attackers direct control over the system's core operations.
Rootkits and Persistent Threats
Hiding in Plain Sight
Kernel-level access is the preferred environment for rootkits and advanced persistent threats (APTs). By embedding themselves deep within the OS kernel, these malicious programs can:
- Hide their processes, files, and network connections from users and security tools.
- Modify system logs to erase traces of their activity.
- Disable security software operating at lower privilege levels.
- Ensure their persistence even after system reboots.
Denial of Service (DoS)
Bringing Systems to a Halt
Exploiting kernel vulnerabilities can crash the entire system or make it unresponsive, leading to a denial of service. Use-after-free conditions or other memory corruption bugs can destabilize the kernel, causing panics or freezes. While perhaps less damaging than data theft, DoS attacks can severely disrupt critical operations.
Bypassing Security Mechanisms
Disabling the Guards
Many security solutions, including antivirus software and EDR systems, require kernel-level access to monitor system behavior effectively. However, this creates a double-edged sword. Malicious software that achieves kernel privileges can potentially target and disable these security tools, blinding the system's defenses before carrying out further attacks.
System Instability and Operational Risk
When Legitimate Software Goes Wrong
The risks aren't limited to malicious attacks. Legitimate software operating at the kernel level, if flawed, can cause significant problems. The global CrowdStrike outage in July 2024 serves as a stark reminder. A faulty update to their security agent, which operates with kernel privileges, caused widespread system crashes (Blue Screens of Death) across millions of Windows machines. This incident highlighted the operational risks associated with granting kernel access, even to trusted security vendors, and sparked debate about the necessity and safety of this approach.
Privacy Concerns
Unfettered Monitoring Capabilities
Software with kernel-level access has the technical capability to monitor virtually all system activity – keystrokes, network traffic, file access, application usage – often without explicit user consent for each action. While legitimate security tools use this for threat detection, the potential for misuse or data leakage raises significant privacy concerns, especially with third-party software.
Visualizing Kernel Threat Severity
Kernel-level exploits present a multifaceted threat landscape. The following chart provides a comparative visualization of the perceived severity associated with different types of outcomes resulting from kernel-level compromises. Severity is assessed based on potential impact on system integrity, data confidentiality, availability, and attacker control.
This visualization underscores that Remote Code Execution and Rootkit/Persistence capabilities are often considered the most severe threats due to the complete control and stealth they offer attackers. However, other impacts like Privilege Escalation, Data Exfiltration, and Security Bypass also represent critical risks inherent to kernel-level access.
Mapping the Kernel Access Landscape
The concept of kernel-level access involves multiple interconnected elements, from the fundamental nature of the kernel to specific vulnerabilities, attack vectors, and mitigation strategies. This mindmap provides a visual overview of these relationships:
This map illustrates how the fundamental power of kernel access creates significant security risks when vulnerabilities are exploited. It also highlights the various strategies employed to defend against these threats.
Illustrating the Architecture
Understanding the separation between user space and kernel space is crucial to grasping the implications of kernel-level access. The following images depict typical operating system architectures, showing the kernel as the central intermediary between applications and hardware.
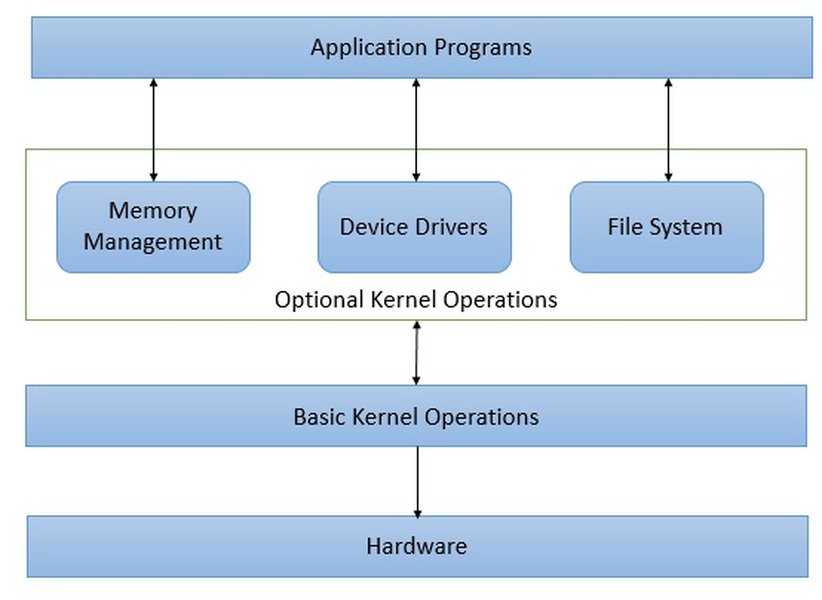
These diagrams typically show applications residing in the less-privileged user space, making requests (system calls) to the kernel. The kernel, operating in the privileged kernel space, fulfills these requests by interacting with hardware or managing resources. Gaining kernel-level access means breaking through this separation and operating within the privileged core.
Notable Kernel Vulnerabilities
Specific vulnerabilities demonstrate the concrete risks associated with kernel access. The table below summarizes some significant examples mentioned in recent security analyses:
| CVE Identifier | Vulnerability Type | Impact | Affected Component / Context | Mitigation / Notes |
|---|---|---|---|---|
| CVE-2024-1086 | Use-after-free | Local Privilege Escalation | Linux Kernel (Netfilter subsystem) | Actively exploited; Patching required. |
| CVE-2024-4011 | Use-after-free | Potential impacts (DoS, Code Execution) | Linux Kernel (Specific versions 5.14.21 to 6.6.14) | Affects Debian, Ubuntu; Patching required. |
| CVE-2022-47939 | Improper Input Validation | Remote Code Execution | Linux Kernel (ksmbd module, SMB2_TREE_DISCONNECT) | Requires ksmbd enabled; Unauthenticated remote attack possible. Patching required. |
| CVE-2016-5195 ("Dirty COW") | Race Condition | Local Privilege Escalation | Linux Kernel (Memory subsystem, Copy-on-Write) | Allowed write access to read-only memory. Patched in later kernel versions. |
| Multiple (e.g., in iwch_cm.c) | Use-after-free | Denial of Service, Potential Code Execution | Linux Kernel (Infiniband driver) | Demonstrates risks in specific hardware drivers. Patching required. |
This table highlights the variety of flaws (memory corruption, logic errors) that can lead to kernel compromise and the severe consequences, ranging from denial of service to full remote control.
Case Study: Kernel Access in Anti-Cheat Software
A prominent area where kernel-level access is frequently utilized, sparking considerable debate, is in anti-cheat software for online gaming. Developers argue this deep system access is necessary to detect sophisticated cheats that operate at a low level to manipulate game processes or memory. However, this practice carries the inherent risks discussed previously.
This video discusses the justifications, privacy concerns, and dangers associated with granting kernel-level access to anti-cheat systems. Critics point out that vulnerabilities in the anti-cheat driver itself could become a vector for malware, and the extensive monitoring raises privacy flags. Furthermore, bugs in these drivers can cause system instability or conflicts with other software. The debate highlights the trade-offs between security/fairness in specific applications and the broader systemic risks of granting kernel privileges to third-party software.
Mitigation Strategies: Defending the Core
Protecting against the threats posed by kernel-level exploits requires a multi-layered defense strategy:
- Timely Updates and Patching: Regularly applying security patches released by OS vendors (like Microsoft, Linux distributions) is the most critical step. This closes known vulnerabilities before attackers can exploit them.
- Kernel Hardening: Configuring the kernel to minimize its attack surface is crucial. This involves disabling unused features, modules, and system calls, and enabling built-in security options (like Control-Flow Integrity or stricter memory permissions).
- Vulnerability Management: Proactively scanning systems for known vulnerabilities and managing the patching process effectively is essential.
- Use of Modern Security Features: Leveraging OS security features like Windows Defender's memory scanning and Virtualization-Based Security (VBS), or Linux security modules (LSMs) like SELinux or AppArmor, adds layers of protection. Secure Boot helps ensure only trusted code loads early in the boot process.
- Principle of Least Privilege: Software should only be granted the minimum privileges necessary for its function. Avoid running applications with unnecessary administrative or kernel access.
- Careful Vetting of Third-Party Software: Scrutinize any software requiring kernel access, especially drivers, security tools, and specialized applications like anti-cheat. Understand the risks involved and consider alternatives if possible.
- Monitoring and Detection: Employ robust system monitoring and EDR solutions capable of detecting anomalous behavior, even potentially originating from compromised kernel components.
The ongoing debate, amplified by incidents like the CrowdStrike outage, also involves OS vendors potentially restricting or changing how third-party software can interact at the kernel level, aiming for a better balance between functionality and security.
Frequently Asked Questions (FAQ)
What exactly is the 'kernel' in an operating system?
The kernel is the core component of an operating system. It acts as a bridge between software applications and the computer's hardware. It manages system resources like the CPU, memory, and peripheral devices, handles task scheduling, and enforces security. All other parts of the OS rely on the kernel to function.
Why do some programs *need* kernel-level access?
Certain tasks require direct interaction with hardware or deep system monitoring that isn't possible from the restricted user space. Examples include:
- Device drivers (for graphics cards, network adapters, etc.) need to talk directly to hardware.
- Some antivirus/EDR solutions need deep inspection capabilities to detect rootkits or intercept malicious system calls.
- Virtualization software needs to manage hardware resources for virtual machines.
- Some system utilities for performance monitoring or disk management require low-level access.
- Kernel-level anti-cheat systems aim to detect cheats operating below the standard application layer.
What is the difference between user-level and kernel-level exploits?
User-level exploits target vulnerabilities in applications running in the user space (e.g., web browsers, office software). They typically grant the attacker control over that specific application or the user's account, but not the entire system.
Kernel-level exploits target vulnerabilities within the OS kernel or kernel-mode drivers. A successful kernel exploit usually grants the attacker the highest level of privilege (root or SYSTEM), allowing complete control over the entire machine.
Can antivirus software protect against all kernel-level threats?
While modern antivirus and EDR solutions often operate with kernel privileges to detect and block threats effectively, they are not foolproof. Sophisticated kernel-level malware (rootkits) can sometimes evade detection or even disable the security software itself. Furthermore, zero-day kernel vulnerabilities (those unknown to vendors) can be exploited before patches or detection signatures are available. Defense-in-depth, including timely patching and kernel hardening, remains crucial.
Is kernel-level access inherently bad?
No, kernel-level access is not inherently bad; it's a necessary feature for operating systems to function and interact with hardware. The issue lies in the *risk* it represents. Any code running at this level, whether legitimate or malicious, has the potential to cause significant harm if it contains bugs, vulnerabilities, or malicious intent. Therefore, granting and managing kernel-level access must be done with extreme caution.
References
- Active Exploitation Of Linux Kernel Privilege Escalation Vulnerability - crowdstrike.com
- The Cybersecurity Professional's Guide to Kernel Exploits - appsecengineer.com
- CrowdStrike and kernel-level access: a deep dive | BCS - bcs.org
- Kernel-Level Access: What it Means for Windows Security - fortect.com
- Multiple Security Vulnerabilities in Linux Kernel - nsfocusglobal.com
- Top 10 Linux Kernel Vulnerabilities You Should Know - mend.io
- Top Linux Security Vulnerabilities and How to Prevent Them - sternumiot.com
Recommended Reading
Last updated April 5, 2025