
Understanding the Dark Web
Exploring the Hidden Corners of the Internet
Key Takeaways
- Anonymity and Privacy: The Dark Web offers users heightened privacy through specialized tools like Tor.
- Diverse Uses: While often associated with illegal activities, the Dark Web also serves legitimate purposes such as secure communication for journalists and whistleblowers.
- Security Risks: Navigating the Dark Web poses significant risks, including exposure to malware, scams, and illegal content.
What is the Dark Web?
A Subset of the Deep Web with Enhanced Anonymity
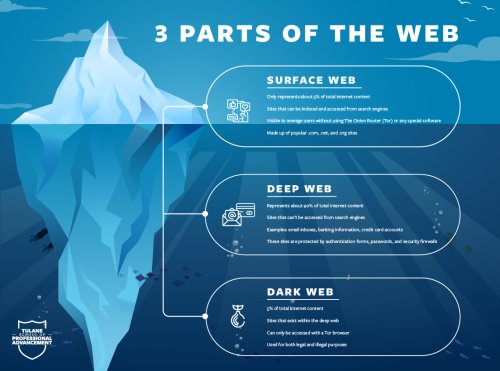
The Dark Web is a concealed segment of the internet that remains inaccessible to standard search engines like Google, Bing, or Yahoo. It is a subset of the broader Deep Web, which encompasses all web content not indexed by traditional search engines, including private databases, academic journals, and subscription-based services. Unlike the Deep Web, the Dark Web is intentionally hidden and requires specific tools and configurations to access.
Accessing the Dark Web
Accessing the Dark Web typically involves using specialized software that anonymizes a user's internet connection. The most common tool for this purpose is the Tor Browser (The Onion Router), which routes internet traffic through a series of servers (nodes) to obscure the user's IP address and location. This layered encryption process ensures that both the user's identity and their browsing activities remain concealed from surveillance and tracking.
Key Tools for Access
- Tor Browser: The most widely used tool for accessing the Dark Web, utilizing the Tor network to provide anonymity.
- I2P (Invisible Internet Project): An alternative network that emphasizes internal anonymity and is used for hidden services.
- Freenet: A decentralized platform designed for censorship-resistant communication and publishing.
.onion Domains
Websites on the Dark Web often use the ".onion" domain extension, which signifies that they are accessible only through the Tor network. These domains are not part of the standard Domain Name System (DNS) and are generated automatically, making them difficult to trace. Each .onion address is typically a string of seemingly random characters, enhancing the anonymity of both the site and its users.
Purpose and Usage
Legitimate Uses
While the Dark Web is frequently associated with illicit activities, it also serves several legitimate and important functions:
- Secure Communication: Journalists, whistleblowers, and activists use the Dark Web to communicate sensitive information without fear of surveillance or retribution.
- Bypassing Censorship: In regions with strict internet censorship, individuals use the Dark Web to access and share information freely.
- Privacy Protection: Users concerned about online privacy leverage the Dark Web to shield their activities from tracking and data collection.
Illicit Activities
Despite its legitimate uses, the Dark Web is also a hotspot for various illegal and unethical activities:
- Black Markets: Platforms for buying and selling illegal goods such as drugs, weapons, and counterfeit currency.
- Cybercrime: Services and tools for hacking, distributing malware, and conducting financial scams are prevalent.
- Stolen Data: Personal information, credit card details, and other sensitive data are frequently traded or sold.
- Extremist Content: The Dark Web hosts forums and sites that promote extremist ideologies and illegal content.
Technical Characteristics
Anonymity and Encryption
The Dark Web's infrastructure is built upon robust encryption and routing mechanisms that ensure user anonymity:
- Layered Encryption: Data is encrypted multiple times and routed through various nodes to prevent tracing.
- Decentralized Networks: Unlike the surface web, the Dark Web operates on decentralized networks, reducing the risk of centralized surveillance.
Infrastructure
The underlying infrastructure of the Dark Web contributes to its security and anonymity:
- Darknets: Overlay networks that utilize the internet but require specific software and configurations to access.
- Tor Nodes: Relays that transport encrypted data, obscuring the origin and destination of internet traffic.
Origins of the Dark Web
The Dark Web's origins can be traced back to the early 2000s when the U.S. Navy developed the Tor project to protect government communications. Subsequent projects like Freenet and I2P further advanced anonymous networking, laying the groundwork for the modern Dark Web. Over time, these technologies became accessible to the general public, expanding the Dark Web's user base and solidifying its presence as a significant part of the internet.
Dark Web vs. Deep Web
Understanding the Distinction
It's crucial to differentiate between the Dark Web and the Deep Web, as they are often confused:
| Aspect | Deep Web | Dark Web |
|---|---|---|
| Definition | All parts of the internet not indexed by standard search engines, including private databases and subscription sites. | A subset of the Deep Web, intentionally hidden and accessible only through specialized tools like Tor. |
| Accessibility | Accessible via standard browsers with the right credentials or permissions. | Requires anonymizing software and specific configurations to access. |
| Content | Includes academic resources, private networks, medical records, and more. | Hosts both legitimate services like secure communication platforms and illicit activities such as black markets. |
| Security | Generally secure but varies based on the specific content and access controls. | Highly secure in terms of anonymity but poses significant risks due to the nature of some hosted content. |
Uses of the Dark Web
Legitimate Applications
The Dark Web serves several legitimate purposes that contribute to privacy, security, and freedom of information:
- Whistleblowing Platforms: Secure channels for individuals to report misconduct without fear of exposure.
- Secure Communication: Encrypted communication tools for journalists and activists working in oppressive environments.
- Privacy-Focused Services: Platforms that prioritize user anonymity and data protection, catering to privacy-conscious individuals.
- Research and Collaboration: Academic and professional collaborations that require confidential exchanges of information.
Illicit Applications
Despite its legitimate uses, the Dark Web is notorious for facilitating a range of illegal activities:
- Black Markets: Online marketplaces offering illegal goods such as narcotics, firearms, counterfeit currencies, and stolen data.
- Cybercrime Services: Platforms providing hacking tools, malware, and services for conducting cyberattacks.
- Stolen Personal Information: Trading of personal data, including Social Security numbers, credit card details, and login credentials.
- Extremist Content: Forums and websites promoting extremist ideologies, radicalization, and planning of unlawful activities.
Security Considerations
Risks Involved
While the Dark Web provides enhanced privacy, it also presents several security risks:
- Malware and Scams: High prevalence of malicious software and fraudulent schemes targeting unsuspecting users.
- Legal Consequences: Engagement in illegal activities can lead to severe legal repercussions, including prosecution and imprisonment.
- Data Theft: Vulnerability to data breaches and theft due to the illicit nature of many operations on the Dark Web.
- Surveillance Threats: Law enforcement agencies actively monitor Dark Web activities, increasing the risk of being traced.
Protective Measures
To mitigate risks, users should adopt stringent security practices when navigating the Dark Web:
- Use Reliable Security Software: Employ comprehensive antivirus programs and anti-malware tools to detect and prevent threats.
- Maintain Anonymity: Avoid sharing personal information and use pseudonyms instead of real identities.
- Verify Sources: Be cautious of the legitimacy of websites and services to avoid scams and fraudulent activities.
- Regular Updates: Keep all software, including the Tor browser, updated to protect against known vulnerabilities.
Ethical and Legal Implications
Balancing Privacy and Security
The Dark Web presents a complex interplay between the need for privacy and the potential for illegal activities. On one hand, it empowers individuals to protect their privacy, communicate securely, and access information without restriction. On the other hand, it facilitates criminal enterprises, making it a target for law enforcement and cybersecurity efforts.
Law Enforcement Challenges
Traditional law enforcement techniques are often ineffective on the Dark Web due to its inherent anonymity and encryption. This necessitates the development of specialized cybercrime units and advanced technological tools to investigate and prosecute criminal activities conducted within this hidden part of the internet.
Regulatory Perspectives
Governments and international bodies are continuously grappling with how to regulate the Dark Web. Efforts focus on balancing the protection of individual privacy rights with the need to prevent and combat illicit activities. This includes legislative measures, international cooperation, and the deployment of cyber surveillance technologies.
Future of the Dark Web
Technological Advancements
The Dark Web is likely to evolve alongside advancements in technology. Innovations in encryption, decentralized networks, and anonymous communication protocols will further enhance its privacy features, potentially making it more resilient against surveillance and censorship.
Potential Trends
-
Increased Legitimacy: Greater recognition of the Dark Web's role in protecting free speech and privacy may lead to more legitimate uses and acceptance.
-
Enhanced Security Measures: Development of more robust security protocols to protect users and mitigate risks associated with malicious activities.
-
Regulatory Scrutiny: Intensified efforts by governments to monitor and regulate Dark Web activities, potentially leading to more sophisticated law enforcement strategies.
-
Integration with Emerging Technologies: Incorporation of blockchain, artificial intelligence, and other emerging technologies to improve anonymity and functionality.
Conclusion
The Dark Web represents a significant and multifaceted component of the internet, characterized by its emphasis on anonymity and privacy. While it serves vital roles in protecting free speech, enabling secure communication, and providing a refuge for activists and whistleblowers, it is also a breeding ground for illegal activities and cybercrime. Navigating the Dark Web requires a deep understanding of its technical underpinnings, potential risks, and the ethical considerations it entails. As technology continues to advance, the Dark Web will undoubtedly evolve, presenting both opportunities and challenges for users, law enforcement, and society at large.
References
Last updated February 12, 2025